In the leafy suburbs of northern Virginia, a place ruled by homeowner’s associations with tremendous power to dictate everything from the color of one’s front door to the length of grass in the lawn, something as heinous as garage doors suddenly failing to open on command is sure to cause a kerfuffle. We’ve seen this sort of thing before, where errant RF emissions cause unintentional interference, and such stories aren’t terribly interesting because the FCC usually steps in and clears things up. But this story is a little spicier given the source of the interference: Warrenton Training Center, a classified US government communications station located adjacent to the afflicted neighborhood. WTC is known to be a CIA signals intelligence station, home to spooks doing spooky stuff, including running high-power numbers stations. The interference isn’t caused by anything as cloak-and-dagger as that, though; rather, it comes from new land-mobile radios that the Department of Defense is deploying. The new radios use the 380-400 MHz band, which is allocated to the Federal Government and unlicensed Part 15 devices, like garage door remotes. But Part 15 rules, which are clearly printed on every device covered by them, state that the devices have to accept unwanted interference, even when it causes a malfunction. So the HOA members who are up in arms and demanding that the government buy them new garage door openers are likely to be disappointed.
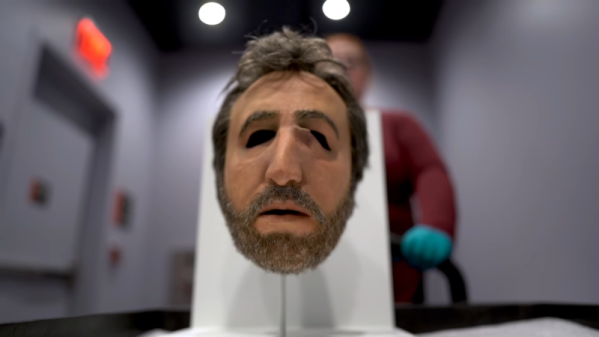
Speaking of spooks, if you’re tired of the prying electronic eyes of facial recognition cameras spoiling your illusion of anonymity, have we got a solution for you. The Opt-Out Cap is the low-tech way to instantly change your face for a better one, or at least one that’s tied to someone else. In a move which is sure not to arouse suspicion in public, doffing the baseball cap deploys a three-piece curtain of semi-opaque fabric, upon which is printed the visage of someone who totally doesn’t look creepy or sketchy in any way. Complete instructions are provided if you want to make one before your next trip to the ATM.
It’s always a great day when a new Ken Shirriff post pops up in our feed, and his latest post is no exception. In it, Ken goes into great detail about the history of the 80×24 (or 25) line standard for displays. While that may sound a bit dry, it’s anything but. After dispelling some of the myths and questionable theories of the format’s origin – sorry, it’s not just because punch cards had 80 columns – he discusses the transition from teletypes to CRTs, focusing on the very cool IBM 2260 Display Station. This interesting beast used an acoustic delay line made of 50′ (15 m) of nickel wire. It stored data as a train of sound pulses traveling down the wire, which worked well and was far cheaper than core memory, even if it was susceptible to vibrations from people walking by it and needed a two-hour warm-up period before use. It’s a fascinating bit of retrocomputing history.
A quick mention of a contest we just heard about that might be right up your alley: the Tech To Protect coding challenge is going on now. Focused on applications for public safety and first responders, the online coding challenge addresses ten different areas, such as mapping LTE network coverage to aid first responders or using augmented reality while extricating car crash victims. It’s interesting stuff, but if you’re interested you’ll have to hurry – the deadline is November 15.
And finally, Supercon starts this week! It’s going to be a blast, and the excitement to hack all the badges and see all the talks is building rapidly. We know not everyone can go, and if you’re going to miss it, we feel for you. Don’t forget that you can still participate vicariously through our livestream. We’ll also be tweet-storming and running a continuous chat on Hackaday.io to keep everyone looped in.