[Will Scott] and [Gabe Edwards] shed some light on the current state of consumer computing technology at 34C3 in their talk DPRK Consumer Technology. The pair has also created a website to act as a clearinghouse for this information — including smartphone OS images up at koreaComputerCenter.org.
Not a whole lot is known about what technology North Korean citizens have available to them. We have seen Red Star OS, the Mac-like Linux based operating system used on PC based desktops. But what about other systems like smartphones?
[Will] and [Gabe] found that cell phones in North Korea are typically manufactured by Chinese companies, running a custom version of the Android Operating system. The phone hardware is common — the phone sold as the Pyongyang 2407 in North Korea is also sold in India as the Genie v5. If you can get your hands on the Genie, you can run the Korean version of the Android OS on that hardware.
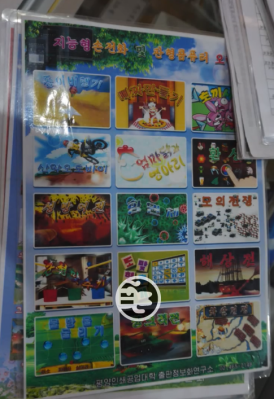
App stores are also different. North Korean Android has no software app store. To buy an app, a user goes to a physical store and picks from a catalog. The store owner then downloads the app to the customer’s phone via a cable.
North Korea places a lot of emphasis on education. Phones and tablets include a number of PDFs for textbooks. You can learn Java, Linux, and other topics. The PDF files are encrypted and locked to a specific device though. [Will] and [Gabe] found that a common library used by the ezPDF Android had been changed. Someone in North Korea had actually gone in and modified the binary to hook a decryption algorithm in the library’s file handling code. The encryption system itself is not too difficult to defeat — a 512 byte XOR pad is hardcoded at the end of the library. The device’s MAC address is used to calculate an offset into that XOR pad and decrypt the file.
[Will] and [Gabe] have just scratched the surface of the available data there is plenty more to be found at koreaComputerCenter.org. Want to know more about Red Star OS? Check out this article!
















“To buy an app, a user goes to a physical store and picks from a catalog. The store owner then downloads the app to the customer’s phone via a cable.”
This tells us all we need to know about them strangle the government has.
I dunno if that’s the best example, though. Fun fact: North Korea used to use rubber bands to restrict radio and TV dials to an official channel (or range of channels, I forget.)
The periodic state inspections would basically just look at stickers along creases in the devices to see if it had been tampered with, but some defectors describe using shims to reach into the case and tune to South Korean or Chinese broadcasts.
I don’t see the hallmarks of a dictatorial regime in that, to be completely honest. It does beg the question why they don’t have their own digital store instead, as they do seem capable enough to do that.
How do you expect them to download apps when only parts of one city have cell service?
It’s about control and information. They want it so the government knows all the apps those allowed to have smartphones have on them. They want to know what PDFs and other documents people are reading on their phones.
With total knowledge, or the attempt at having it, of what everyone is doing, it’s easier to punish those who do things that are not allowed.
https://www.reuters.com/article/us-northkorea-change-insight/the-50-device-that-symbolizes-a-shift-in-north-korea-idUSKBN0MM2UZ20150327
‘raise the question’, not ‘beg the question.’
With enough begging any question can be raised to adulthood.
Great research!
Quite fascinating. It’s like peeking though the iron curtain.
Even if this information is old, it really is difficult for me to believe that DPRK/NK is behind any world-class worm attack spread on the “real” internet.
They claim they used wannacry last, which would be using existing stuff for their own purpose and that is at least easy (although I doubt it was them really).
But they were also blamed for the Sony hack.
Mind you, we were recently reminded that 50% of the people use 123456 as password, so I wonder how many of the Sony executives do that too…
And the so-called ‘security experts’ dong ‘analysis’ for the media and US government would easily describe guessing a simple password as ‘a sophisticated hack only a state actor could do’.
I recently ‘hacked’ into an iPad (so it could be wiped without bricking it) that had 1234 as its lock code. In the past I’ve found two lost cell phones that had 1234 for their lock code.
1234? That’s amazing! I’ve got the same combination on my luggage!
You idiots! These are not them! You’ve captured their stunt doubles!
“The PDF files are encrypted and locked to a specific device though”: What, they’re worried about copyright infringement in a communist country? Are they afraid that the content creator won’t make enough money?
Most likely they want to track who’s got access to that technical information — to keep it from slipping to anti-government entities.
It’s a Communist dictatorship, they just want to control information for the purpose of control, what amazes me is they let people have smart phones, so hackable, hence intolerable.
I’ll bet big brother is watching those phones remotely.
With a rather unpleasant reaction if they ind you doing something they don’t like.
And come on, what’s better than smartphones to control and track people? They are the dream of anybody into that stuff.
Regarding the Indian phone model cited. I don’t think the company is called Genie, but “Gionee”, and the model is the “Gionee Ctrl V5”.
I think you are right, but talking of which:
“In 2014, Gionee was accused by German media of delivering smartphones and tablets with pre-installed malware”
Makes you wonder if the NK also have that issue, malware on their spyware.