CircuitPython is becoming a thing! CircuitPython was originally developed from MicroPython and ported to various ARM boards by Adafruit. Now, SparkFun is shipping their own CircuitPython board based on the nRF52840, giving this board an ARM Cortex-M4 and a Bluetooth radio.
You like contests, right? You like circuit boards too, right? Hackster.io now has a BadgeLove contest going on to create the Blinkiest Badge on Earth. Yes, this is a #badgelife contest, with the goal of demonstrating how much you can do in a single circuit badge. Prizes include a trip to San Francisco, a badass drone, a skateboard, a t-shirt, or socks. YES, THERE ARE SOCKS.
We have a date for the Vintage Computer Festival Pacific Northwest 2019. It’s going down March 23 and 24 at the Living Computers Museum in Seattle. The call for exhibitors is now open so head over and check it out. So far the tentative list of exhibits and presenters include Attack of the SPARC Clones, and I must mention that SPARC systems are showing up on eBay with much higher frequency lately. I have no idea why.
Need another con? How about a KiCAD con? The inaugural conference for KiCAD users is happening next April in Chicago and the call for talk proposals just opened up. The con focuses on topics like using KiCAD in a manufacturing setting, what’s going on ‘under the hood’ of KiCAD, and how to use KiCAD to make an advanced product.
Spanish police have stopped a homemade scooter. Someone, apparently, was tearing around a public road in Galacia on a homemade scooter. From the single picture, we’re going to say ‘not bad.’ It’s a gas-powered weed wacker mounted to a homemade frame.
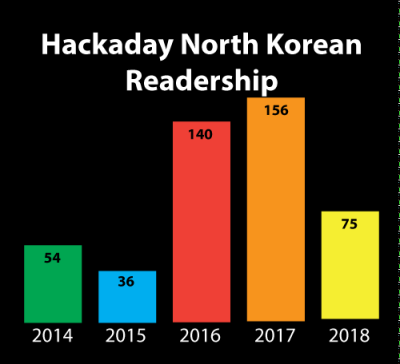 Every year, in December, we take a look back at what Hackaday has accomplished in the past twelve months. Sure, we gave out hundreds of thousands of dollars in awards in the Hackaday Prize, and yes, we’ve pushed our coverage of tech advancements into weird, uncharted, but awesome territory. Our biggest accomplishment, though, is always how many readers we reach. This year, we had a slight fall-off in our readership in the Democratic People’s Republic of North Korea. We’re down from 156 views in 2017 to 75 views this year. While the year isn’t over, we don’t expect that number to change much. What was the cause of this drop-off? We’re not quite sure. Only time will tell, and we’re looking forward to serving fresh hacks every day to the DPRK in 2019.
Every year, in December, we take a look back at what Hackaday has accomplished in the past twelve months. Sure, we gave out hundreds of thousands of dollars in awards in the Hackaday Prize, and yes, we’ve pushed our coverage of tech advancements into weird, uncharted, but awesome territory. Our biggest accomplishment, though, is always how many readers we reach. This year, we had a slight fall-off in our readership in the Democratic People’s Republic of North Korea. We’re down from 156 views in 2017 to 75 views this year. While the year isn’t over, we don’t expect that number to change much. What was the cause of this drop-off? We’re not quite sure. Only time will tell, and we’re looking forward to serving fresh hacks every day to the DPRK in 2019.