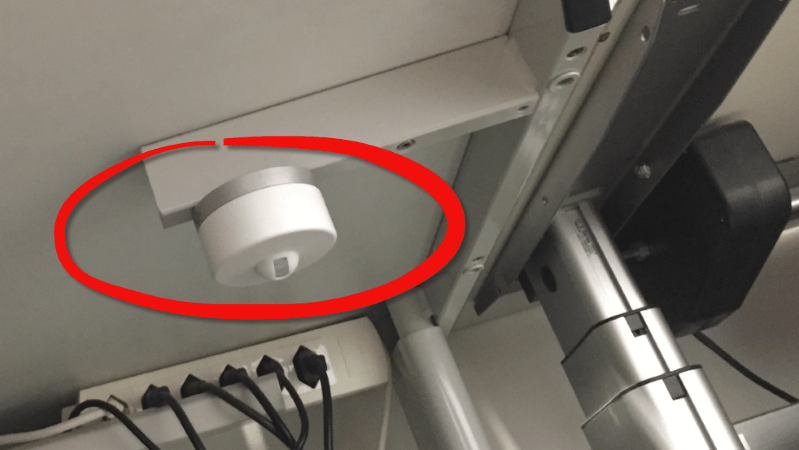
There are a lot of bad days at work. Often it’s the last day, especially when it’s unexpected. For the particularly unlucky, the first day on a new job could be a bad day. But the day you find an unknown wireless device attached to the underside of your desk has to rank up there as a bad day, or at least one that raises a lot of serious questions.
As alarming as finding such a device would be, and for as poor as the chain of decisions leading these devices being attached to the workstations of the employees at a mercifully unnamed company, that’s not the story that [Erich Styger] seeks to tell. Rather, this is a lesson in teardown skills – for few among us would not channel the anger of finding something like this is into a constructively destructive teardown – and an investigation into the complete lack of security consideration most IoT devices seem to be fielded with these days.
Most of us would recognize the device as some kind of connected occupancy sensor; the PIR lens being the dead giveaway there. Its location under a single person’s desk makes it pretty clear who’s being monitored.
The teardown revealed that the guts of the sensor included a LoRa module, microcontroller, a humidity/temperature sensor, and oddly for a device apparently designed to stick in one place with magnets, an accelerometer. Gaining access to the inner workings was easy through the UART on the microcontroller, and through the debug connectors and JTAG header on the PCB. Everything was laid out for all to see – no firmware protection, API keys in plain text, and trivially easy to reflash. The potential for low-effort malfeasance by a compromised device designed to live under a desk boggles the mind.
The whole article is worth a read, if only as a lesson in how not to do security on IoT devices. We know that IoT security is hard, but that doesn’t make it optional if you’re deploying out in the big wide world. And there’s probably a lot to learn about properly handling an enterprise rollout too. Spoiler alert: not like this.















Still not as bad as smart wifi plug (which can turn on/off connected device) which sends your wifi ssid and password in cleartext over tcp every 60s to a server in china.
Care to give a little more details/link to article about that particular wifi switch?
Ogemray wifi plug GWF-SU01-RE. I have checked it myself for security evaluation at my company. It was rejected because of this problem.
I’ve considered networking my entire house for automation. Wireless is the easy route, but I’ve had security concerns, doubly so with off the shelf parts. I have two LAN wired outdoor security cameras that I found out connected to Chinese servers, but only because I inspected the firmware. I had to isolate them on my network because I became paranoid, then took out my inside cameras and replaced them with something custom made.
I figured that if I’m ever going to do it, it’s going to be a fully secured wired setup, but it’s a logistical PITA that I can’t convince myself to actually do. Yet.
If you can connect to your off-the-shelf camera from internet, typically it’s relayed through some servers. What’s funny, it’s easier for manufacturers to do than ask users to open some ports in their home router and typically works.
UPnP is usually good enough to get appropriate ports opened. The stumbling block would be that most users don’t have a well known hostname on the internet.
Actually, depending on the connection method, relaying via a server may be the cheaper and more practical option. Say you’re running a construction company. You want to put up a webcam watching the construction site. You probably don’t have a fixed Cable/DSL line available with a real-world IP. You’ve probably got a cellular connection, which is behind a layer or two of NAT. If I want a public IP on my cellular connection, I’ve got a one time fee of $500 or more each just to provision it, on top of monthly fees. I might have 5 or 6 construction sites going. With a web server elsewhere, I don’t have to worry about dynamic DNS, and have one portal that I can go to to access ALL my cameras, regardless how each is getting to the internet.
Other than wifi, you can drastically reduce your area of attack by using a mesh network. Granted, it does not support hand bandwidth / low latency devices like cameras, but it reduces it to one hub device you manage, rather than tens of devices
ha! I got one of those devices at Home Depot a few years ago.
If you ever find something like this under your desk at work, LEAVE. Leave now, tell them to F off, and never come back. Seriously. You’re better off living on the street.
The accelerometer, by the way, is probably there to detect that the slave has discovered the device and carries it around with him so it thinks he’s at this desk all day.
If your employer is doing this to you, it’s time to burn down the building. Metaphorically, I mean. I would never advocate arson.
Full heartedly agreed. The only teardown necessary is one of the brains of your boss there. Zero reason to stay at such a company, full stop.
Surely you’d want to have some fun hacking ALL the desk sensors in the office before you left?
Make a hardware version of mouseWiggle.exe?
Like this: https://www.youtube.com/watch?v=ebsOm6169Mo
Easy: USB fan & a small cat toy (think duster on a wire) above an up-turned optical mouse.
better solution: no drivers needed or programs to install. works as a “USB HID”: http://wizworks.net/busy-bee
Absolutely agree. If they don’t trust you, you can’t trust them.
But they do trust you, didn’t you read the article, everything in the device was out in the open.
Ask generation Facebook. They do a daily online soul striptease on FB readable by the whole world. Why should they care about such a thing?
https://community.highlandarrow.com/file/bf62167eff3d579936c4e41c1976792ea3f312cfade8b63cb10e3232d99cf0d5.jpg
Thank you for calling the Pizza Hut customer satisfaction hotline. 8-}
Obviously when queried, both sides will say there’s no reason to call their trustworthiness into question.
The accelerometer is clearly there to detect that you are slamming your fists on your desk in frustration. Less then 1 hit per day? Put more work on this drone.
as mentioned below, could the accelerometer not be used to detect movement on the top of the desk? like typing, picking up and putting down a coffee cup?
The accelerometer is probably there because it was cheaper to buy a generic part or copy the whitepaper design than to custom design one without it.
I’m sorry if you’ve had a bad experience with your employer/s in the past. Just to offer an alternative point of view, I will say my company has used these (or similar). They allow for a fairly flexible schedule of working from home or at the office. They used these sensors to get an idea of how many desks were actively in use (had a person in them) at least 3 days a week. For users that aren’t in the office at least 3 days a week they can use ‘hotel cubes’ or have the option to work entirely remote.
They still base performance reviews on quality/quantity of work done, and not where you are to perform said work. The devices were/are useful when it comes to making determinations on how much leased space they need or if/when they need to build a new office.
Maybe my company is the exception, (they’re by far the best place I’ve ever worked in my 20 years in IT), but sensors don’t have to be used for evil.
Get out of here with your rational insight
Logging whether users are in the office… Couldn’t you do the same with a keycard system? Easier, less hardware, less potential for employer mischief.
It’s not about whether they’re in the building, but whether they’re at their desks.
hrm, what about meetings?
Might be legit for surveying desk occupancy for the purposes of optimizing number of desks in a biz with flex work conditions, but finding it under one instead of all or at least a more statistically sound sample indicates this is more likely an HR matter.
At my prior job, I spent time at my desk researching, coding, and debugging, but also spent time in a lab, or seeking out other people in the building to examine problems they had (be it coding, or running through systems with someone in failure analysis).
And of course, meetings.
The accelerometer is there to determine how often you raise/lower your stand up desk. Stand up desks are more expensive, and if employees aren’t using them, it’s not worth outfitting a building with them.
It’s a weird industry that wants to measure “office utilization”. Another comment found the company: https://thingdust.com/
I was pitched by a startup that wanted to measure “desk utilization”, basically how many desks were empty in a shared office (no assigned desk). This could be a malicious spy gadget or more likely a lazy attempt by office managers to know when they’re running out of desk space.
A PIR at every desk was basically the solution. Add a accelerometer to measure you tapping on your keyboard incase the PIR doesn’t work.
walk into the office … swipe your badge at the front door (identity), swipe at the elevator (identity), open your laptop (wifi pinged), reserve a room (location/identity)…. if you’re worried about a PIR sending a 0 or a 1 to the cloud regarding shared desk use so the real estate team can know if they need to order more furniture, you’re paranoid. If you think desk occupancy sensors are used for tracking personal time/identity, you need to be aware that you already gave all that data the second you turned on your computer or walked in the door.
The accelerometer is probably there to alert them if the device (or the desk it is attached on) is moved.
The rest shitshow is a warning of what privacy/IT security nightmare we are waking into with thes IoT devices…
“oddly for a device apparently designed to stick in one place with magnets, an accelerometer.”
Because fitting it to a door, movable whiteboard, or any other number of items in a office which are regularly moved (even when they shouldn’t be) wouldn’t make sense?
Also I think I’ve identified the company from that url snippit, and reverse image search…. So much for keeping that secret eh ;)
Hah. I just checked the dude’s LinkedIn. Seemed easier.
Though I have worked with many ex-[ThatCompany] employees, I have a hard time believing that specific HR dept would be *that* naive.
And on reading the article linked, I get the “impression” that the device was gifted to Erich to reverse eng.
Not so much placed under his desk. Infact, there’s a lot of ambiguity, so I’m not really sure where it’s from..!
He was working at a certain company until April, I wonder if this had anything to do with his leaving?
Also wen fitted to an adjustable height desk, as it appears to be under in the photo, one would have data on how often the height is adjusted.
Thomas Edison was faced with a similar problem, and hacker that we was, beat it (for a time). https://www.gjenvick.com/Biography/ThomasAEdison/05-TheBoyTelegraphOperator.html
Seems like that person doesn’t approve of not locking down stuff, and doesn’t find this a disgusting practice…
Well this person found out what the device was actually being used for, the practice was not disgusting. Monitoring the occupancy of common rooms is a worthwhile goal.
If the intentions were so benign, a heads-up before installing it could have gone a long way. I certainly would appreciate it a lot more than finding it surreptitiously tucked under my desk.
“Everything was laid out for all to see – no firmware protection, API keys in plain text, and trivially easy to reflash.”
So with physical access, you could alter the functionality of the device? I fail to see any fail here. After all, you could just replace the whole PCB if you really wanted, to add some real potential like WLAN sniffing and microphone.
Half the time hackaday applauds manufacturers that make it easy to repurpose devices like this, half the time they call them out on bogus “security issues”.
Have to agree, I don’t see the fail here? It’s an occupancy detector and environmental sensor, using LoRA…
The only real WTF here is that it was deployed under a persons assigned desk without their specific knowledge… TBH, in a flex workspace I see this as perfectly acceptable–you can know how many workspaces are in use, when they were last used, etc… same for conference rooms.
How not to hide company information :
The autor hides the name of the company but a single google search on the not hidden part of the link (or on the picture of the device) leads you to the website : https://www.google.com/search?q=site+“demo.cust.prod”
Here I do wonder if the accelerometer could gather data about vibrations from the desk.
If it has sufficient resolution, then maybe it could provide sufficient data to discern keystrokes from each other.
And that opens up a whole can of worms in terms of IT security.
Though, likely not process the analysis on the device itself, after all, it has a long range transmitter. Not particularly fast, but the night is long.
But yes, logging activity and storing it for a nightly transfer would be very obvious if the device spills its code without even the slightest of security measures to keep its activity a secret.
Also to detect if it was moved, say to another desk, so that one person could keep multiple monitors registering.
One thing that wasn’t mentioned, but probably should: How would this sort of thing look to a person who wears a skirt at work? To someone that doesn’t know technology better, this could look like the boss installed a camera in a perfect place to get very inappropriate and compromising pictures of the employees.
It’s just bad form all around to do this sort of employee monitoring, in my opinion. I’ve always been of the mindset that if a person was hired to do a certain job, and they are indeed capable of doing said job, they should be left alone to do their work in peace.
Uh huh. Your mind went right to that huh?! What are you really thinking?
J/K
I could see someone having that concern. Even if it were a camera though I don’t think it would actually capture anything. It would have to be a pretty short skirt if the thing is mounted to the desk. Not really typical office attire. Otherwise it would just be taking pictures of the skirt. Maybe if it were mounted to the wall a bit lower than the desk or definitely if it were on the floor that would be a problem.
Still not cool though.
“Your mind went right to that huh?! What are you really thinking?”
No more kilts to work?
Just a FYI, different people are of different sizes and appropriate dress code is considerably different in different areas of the world. Also, clothes tend to bunch up and move around when one is seated, maybe the objective is not people wearing skirts but people with pants that are tight in the crotch (irrelevant of gender). Anything, and i repeat ANYTHING located under the desk that could be considered a sensor is wrong and improper, If the objective cannot be achieved from above the desk then it should not be implemented. No one wants something or someone staring at their private parts regardless of clothing being worn
Many people believe that automatic flushing toilets have cameras and can record whatever is there to see. Same suspicion.
When the university remolded the bathrooms in the engineering building, they installed the automatic flushing urinals.
Someone printed vinyl stickers and placed them next to the sensors:
Pictures are for research purposes only
-Trojan
You’ve spent too much time thinking this through.
accelerometer? That’s easy. To notify those monitoring the device that it has been moved.
+1
Exactly, my first thought to hack it would be to move it to the desk of some other guy who’s going to be there all day!
The other issues of note here relate to game theory. The sensor has been deployed to redress the information asymmetry that compromises the manager’s ability to have perfect knowledge of the contracted worker’s work output. Oversight has costs, and may exceed losses from shirking by the contracted worker. A reliance on professionalism in the worker and aggregate measures of productivity have been the traditional mechanisms relied on by “professional managers” to ensure workers are not shirking, but the low costs of IoT devices of this nature and pervasive internet connected devices, i.e. phones, fitbits, work computers, etc… makes me wonder if routine, invasive monitoring of workers will be the new normal…
Well, since workers WILL try to shirk their jobs, it forces the manager team to devise new forms of monitoring. Then workers devise new forms of shirking , he he.
But the inefficiency of that system is that the worker may be in its desk all the time, but just wasting time with facebook/whatsapp/whatever instead of working, and that sensor will not be able to differentiate this.
Better solutions ? With reasonable expectatives in the amount of work to be done, and proportional pay in cases of too few work being done, can manage it. The exceptionally good guy that finishes his work early could go home earlier also, As a lot of solutions, this would work well for some people, while others would use it as reasons to flee from work early, promising they would do more “tomorrow” .
If the manager can’t tell the work output without electronic spying aids, then he/she isn’t a good manager.
Yup, just fire the person who’s produced nothing at the end of the day. ;-)
Buy yourself a watch winder. Place device in watch winder. Hide watch winder in ceiling. Mess with the borg’s mind.
Wrap it in a deflated Mylar balloon, move it to your supervisor’s desk, and unwrap.
Optional: get alerts when they leave their desk!
Showed this to a coworker, and (after checking under our desks for said device) he said he worked for a place that had these, except they were connected to the surge protector under the desk, and when you were away for a certain amount of time it’d cut the power to the desk lamp(s) and computer monitors that people liked to leave on all the time.
For anyone curious, the company in question is “Thingdust”: https://thingdust.com/
Might also be useful for alerting activity on a workstation when there is NO living, breathing human present at said workstation.
Ironically, it might be more useful for Japanese salaryman that are known to over work themselves to death. The major medical causes of these deaths are heart attack and stroke due to stress and a starvation diet.
I guess the accelerometer is a used as a tamper detection mechanism, but if used in a fixed location under a desk, if sensitive enough it could be used as a keylogger with some work. And this is even more worrying.