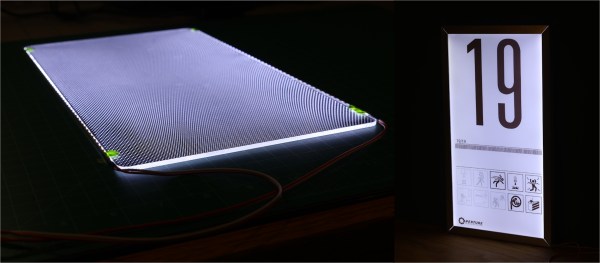
Last year, I found myself compelled to make a scaled-down replica of the iconic test chamber signs from the video game Portal. If you’ve played the game, you’ll remember these signs as the illuminated monoliths that postmarked the start of every test chamber. In hyperstylized video game fashion, they were also extremely thin.

True to the original, my replica would need to be both slimmed down and backlit with a uniform, natural white glow. As fate would have it, the crux of this project was finding a way to do just that: to diffuse light coming in from the edges so that it would emit evenly from the front.
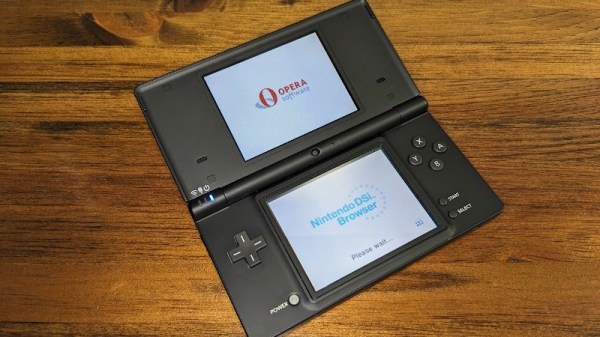
What I thought would be quick project ended up being a dive down the rabbit hole that yielded some satisfying results. Today, I’d like to share my findings and introduce you to light guide plates, one of the key building blocks inside of much of today’s backlit screen technology. I’ll dig into the some of the working principles, introduce you to my homebrew approach, and leave you with some inspirational source code to go forth and build your own. Continue reading “A Hacker’s Introduction To DIY Light Guide Plates”