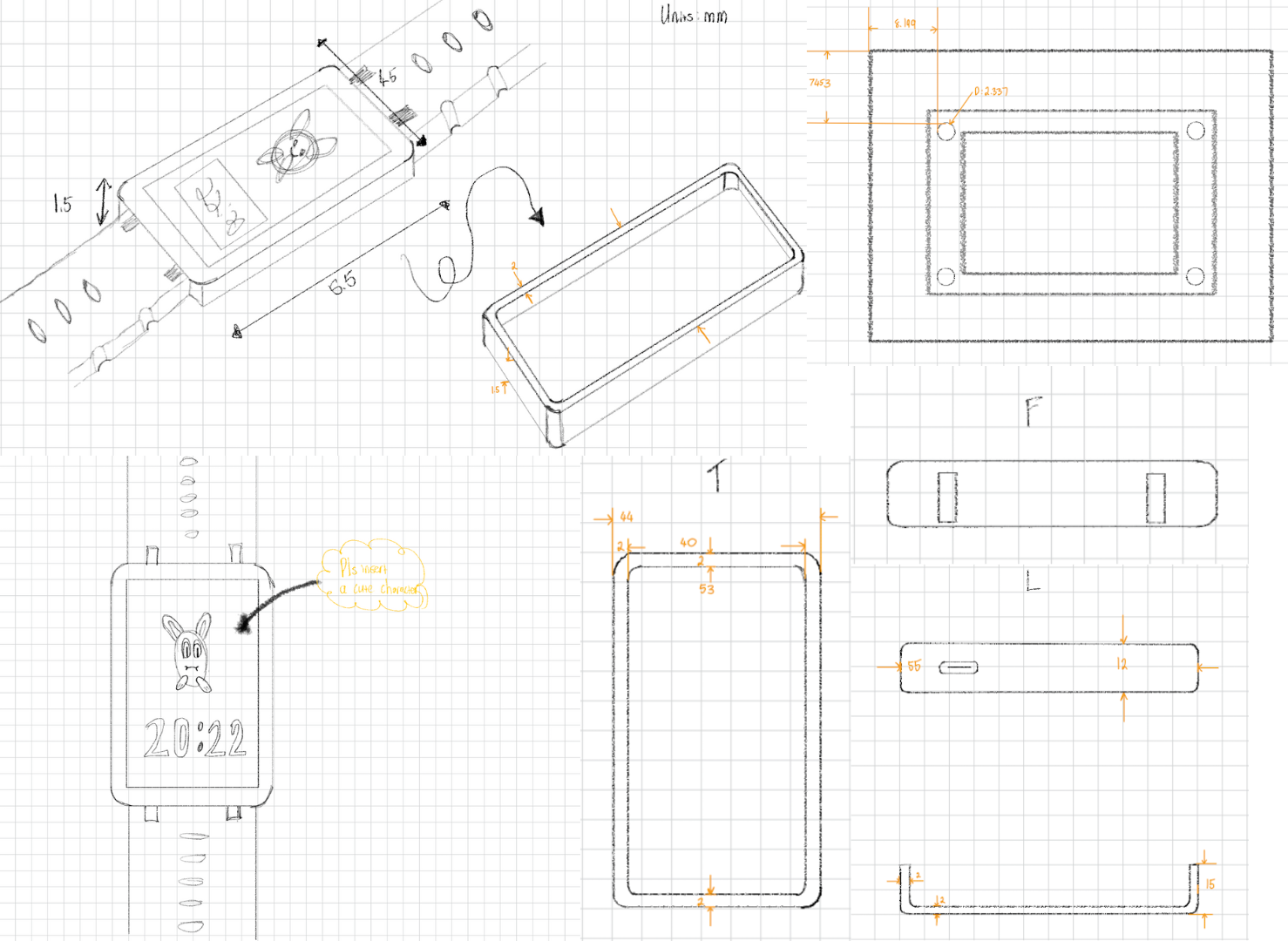
The original ESP32 may be a little long in the tooth by now, but it remains a potent tool for connected devices. We were drawn to [Max Pflaum]’s ESP32 Dashboard as a great example, it’s an ESP32 hooked up to an e-paper display. The hardware is simple enough, but the software is what makes it interesting.
This is deigned as a configurable notification tool, so to make it bend to the user’s will a series of widgets can be loaded onto it. The device runs MicroPython, making it easy enough to write more than the ones already on place. The screen is divided into four zones, allowing for a range of widgets to be used at once. All the details can be found in a GitHub repository.
We like it for its configurability and ease of programming, and because it delivers well on the promise of a useful device. An ESP32 and e-ink combination with MicroPython apps is something we’ve seen before in the world of badges.