To a radio amateur who received their licence decades ago there is a slightly surreal nature to today’s handheld radios. A handheld radio should cost a few hundred dollars, or such was the situation until the arrival of very cheap Chinese radios in the last few years.
The $20 Baofeng or similar dual-bander has become a staple of amateur radio. They’re so cheap, you just buy one because you can, you may rarely use it but for $20 it doesn’t matter. Most radio amateurs will have one lying around, and many newly licensed amateurs will make their first contacts on one. They’re not even the cheapest option either, if you don’t mind the absence of an LCD being limited to UHF only, then the going rate drops to about $10.
The Baofengs and their ilk are great radios for the price, but they’re not great radios. The transmitter side can radiate a few too many harmonics, and the receivers aren’t the narrowest bandwidth or the sharpest of hearing. Perhaps some competition in the market will cause an upping of the ante, and that looks to be coming from Xiaomi, the Chinese smartphone manufacturer. Their Mijia dual-band walkie-talkie product aims straight for the Baofeng’s jugular at only $35, and comes in a much sleeker and more contemporary package as you might expect from a company with a consumer mobile phone heritage. Many radio amateurs are not known for being dedicated followers of fashion, but for some operators the sleek casing of the Mijia will be a lot more convenient than the slightly more chunky Baofeng.
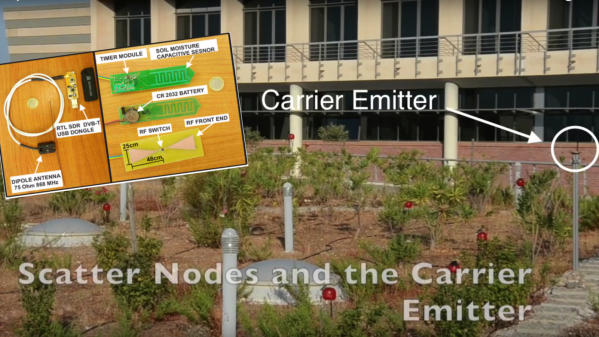
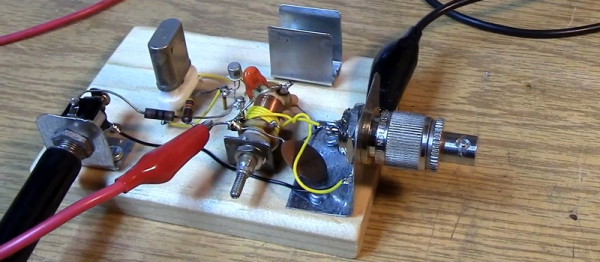
This class of radio offers more to the hardware hacker than just an off-the-shelf radio product, at only a few tens of dollars they become almost a throwaway development system for the radio hacker. We’ve seen interesting things done with the Baofengs, and we look forward to seeing inside the Xiaomi.
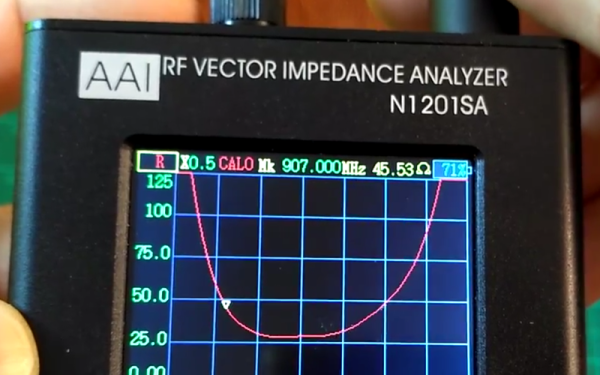
We brought you a look at the spurious emissions of this class of radio last year, and an interesting project with a Baofeng using GNU Radio in a slightly different sense to its usual SDR function.
[via Southgate ARC]