Most of you know how an NFC tag works. The reader creates an RF field that has enough energy to power the electronics in the tag; when the tag wakes up, two-way communication ensues. We’re accustomed to blank tags that can be reprogrammed, and devices like the Flipper Zero that can emulate a tag. In between those two is [MCUer]’s power-free tag emulator, a board which uses NFC receiver hardware to power a small microcontroller that can run emulation code.
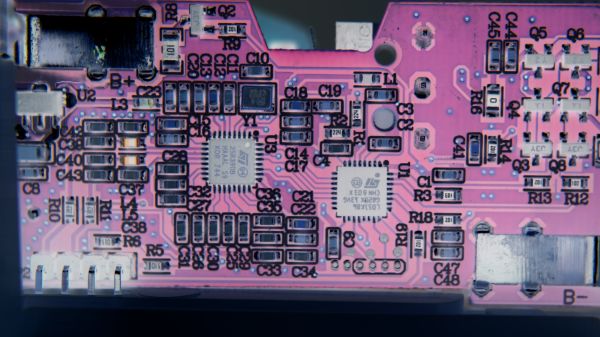
The microcontroller in question is the low-power CW32L010 from Wuhan Xinyuan Semiconductor, a Chinese part with an ARM Cortex M0+ on board. Unfortunately, that’s where the interesting news ends, because all we can glean from the GitHub repository is a PCB layout. Not even a circuit diagram, which we hope is an unintended omission rather than deliberate. It does, however, lend itself to the fostering of ideas, because if this designer can’t furnish a schematic, then perhaps you can. It’s not difficult to make an NFC receiver, so perhaps you can hook one up to a microcontroller and be the one who shares the circuit.