Scientific calculators are an amazing invention that take pocket calculators from being merely basic arithmetic machines to being pocket computers that can handle everything from statistics to algebra. That said, there are a few layers of scientific calculators, starting with those aimed at students. This is where Casio is very popular, especially because it uses traditional algebraic notation (VPAM) that follows the written style, rather than the reverse-polish notation (RPN) of HP and others. However, much like retro Casio wristwatches, it appears that these Casio calculators are now being (poorly) faked, as explained by [Another Roof] on YouTube.
The advanced fx-991 models are updated every few years, with the letters following the model indicating the year, such as fx-991EX standing for the 2015-released model. This was the model that got purchased online and which turned out to be fake. While the fx-991CW is newer, it changes the entire interface and is rightfully scolded in the video. Arguably this makes it the worst Casio scientific calculator in history.
Continue reading “The Rise Of Fake Casio Scientific Calculators”




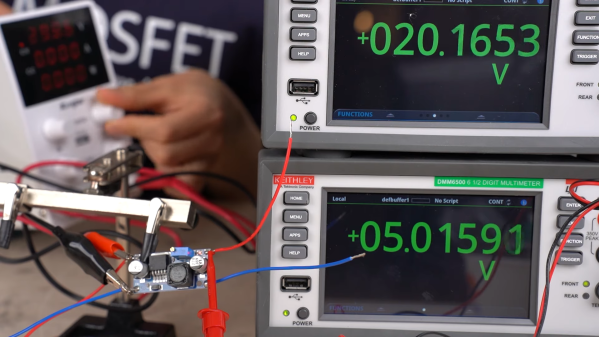
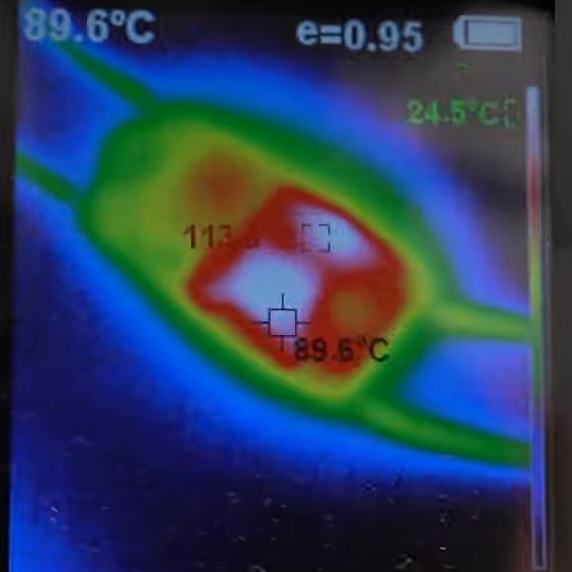 Or do you? It’s not so clear after watching [Denki Otaku]’s video on a bargain bag of buck converters he got from Amazon — ¥1,290 for a lot of ten, or $0.85 a piece. The thing that got [Denki]’s Spidey senses tingling is the chip around which these boards were built: the LM2596. These aren’t especially cheap chips; Mouser lists them for about $5.00 each in a reel of 500.
Or do you? It’s not so clear after watching [Denki Otaku]’s video on a bargain bag of buck converters he got from Amazon — ¥1,290 for a lot of ten, or $0.85 a piece. The thing that got [Denki]’s Spidey senses tingling is the chip around which these boards were built: the LM2596. These aren’t especially cheap chips; Mouser lists them for about $5.00 each in a reel of 500.













