[River] is a big fan of home automation. After moving into a new house, he wanted to assimilate two wirelessly controlled fan lights into his home automation system. The problem was this: although the fans were wireless, their frequency and protocol were incompatible with the home automation system.
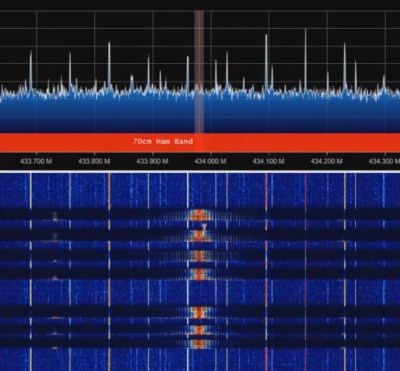
Step one was to determine the frequency the fan’s remote used. Although public FCC records will reveal the frequency of operation, [River] thought it would be faster to use an inexpensive USB RTL-SDR with the Spektrum program to sweep the range of likely frequencies, and quickly found the fans speak 304.2 MHz.
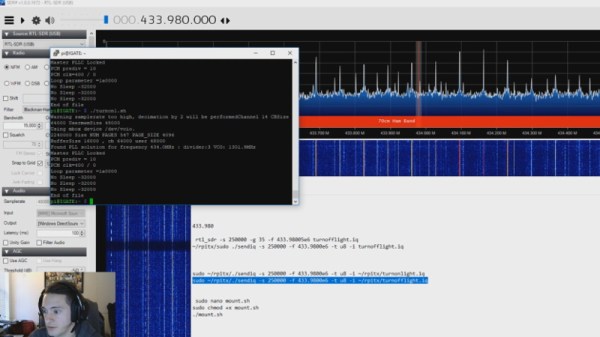
Next was to reverse-engineer the protocol. Universal Radio Hacker is a tool designed to make deciphering unknown wireless protocols relatively painless using an RTL-SDR. [River] digitized a button press with it and immediately recognized it as simple on-off keying (OOK). With that knowledge, he digitized the radio commands from all seven buttons and was quickly able to reverse-engineer the entire protocol.
[River] wanted to use a Raspberry Pi to bring the fans into his home automation system, but the Raspberry Pi doesn’t have a 304.2 MHz radio. What it does have is user-programmable GPIO and the rpitx package, which converts a GPIO pin into a basic radio transmitter. Of course, the Pi’s GPIO pin’s aren’t long enough to efficiently transmit at 304.2 MHz, so [River] added a proper antenna, as well as a low-pass filter to clean up the transmitted signal. The rpitx package supports OOK out of the box, so [River] was quickly able get the Pi controlling his fan in no time!
If you’d like to do some more low-cost home automation, check out this approach to using a Raspberry Pi to control some bargain-bin smart plugs.