Signals Intelligence (SIGINT) refers to performing electronic reconnaissance by eavesdropping on communications, and used to be the kind of thing that was only within the purview of the military or various three letter government agencies. But today, for better or for worse, the individual hacker is able to pull an incredible amount of information out of thin air with low-cost hardware and open source software. Now, thanks to [Josh Conway], all that capability can be harnessed with a slick all-in-one device: the RadioInstigator.
In his talk at the recent 2019 CircleCityCon, [Josh] (who also goes by the handle [CrankyLinuxUser]) presented the RadioInstigator as an affordable way to get into the world of wireless security research beyond the traditional WiFi and Bluetooth. None of the hardware inside the device is new exactly, it’s all stuff the hacking community has had access to for a while now, but this project brings them all together under one 3D printed “roof” as it were. The end result is a surprisingly practical looking device that can be used on the go to explore huge swaths of the RF spectrum at a cost of only around $150 USD.
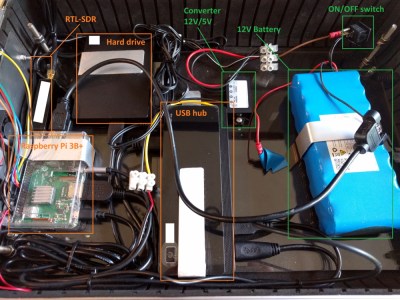
 So what has [Josh] packed into this wireless toybox? It will probably come as little surprise to find out that the star of the show is a Raspberry Pi 3 B+, combined with a touch screen display and portable keyboard so the user can interface with the various security tools installed.
So what has [Josh] packed into this wireless toybox? It will probably come as little surprise to find out that the star of the show is a Raspberry Pi 3 B+, combined with a touch screen display and portable keyboard so the user can interface with the various security tools installed.
To help the RadioInstigator surf the airwaves there’s an RTL-SDR and a 2.4 Ghz nRF24LU1+ “Crazyradio”, both broken out to external antenna connectors on the outside of the device. There’s even an external SMA connector hooked up to the Pi’s GPIO pin, which can be used for low-power transmissions from 5 KHz up to 1500 MHz with rpitx. Everything is powered by a beefy 10,000 mAh battery pack which should give you plenty of loiter time to perform your investigations.
[Josh] has also written several Bash scripts which will get a trove of radio hacking tools installed on the Pi automatically, either by pulling them in through the official repositories or downloading the source and compiling them. Getting the software environment into a known-good state can be a huge time sink, so even if you don’t build your own version of the RadioInstigator, his scripts are still worth checking out.
You can do some pretty incredible things with nothing more than a Pi and an RTL-SDR, but we can’t help but notice there’s still plenty of room inside the RadioInstigator for more gear. It could be the perfect home for a Mult-RTL setup, or maybe even a VGA adapter for spoofing cell networks.
Continue reading “Mobile SIGINT Hacking On A Civilian’s Budget” →