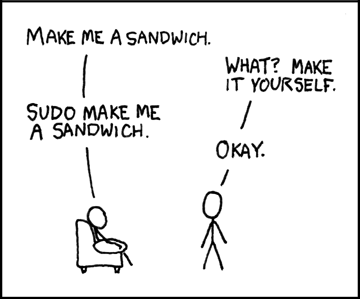
We’ll start this week off with a bit of controversy from Linux Land. Anyone who’s ever used the sudo command knows that you don’t see any kind of visual feedback while entering your password. This was intended as a security feature, as it was believed that an on-screen indicator of how many characters had been entered would allow somebody snooping over your shoulder to figure out the length of your password. But in Ubuntu 26.04, that’s no longer the case. The traditional sudo binary has been replaced with a one written in Rust, which Canonical has recently patched to follow the modern convention of showing asterisks on the password prompt.
As you might expect, this prompted an immediate reaction from Linux greybeards. A bug report was filed just a few days ago demanding that the change be reverted, arguing that breaking a decades-old expectation with no warning could be confusing for users. The official response from a Canonical dev was that they see it the other way around, and that the change was made to improve the user experience. It was also pointed out that those who want to revert to the old style of prompt can do so with a config change. The issue was immediately marked as “Won’t Fix”, but the discussion is ongoing.
Speaking of unexpected changes, multiple reports are coming in that the February security update for Samsung Galaxy devices, which is currently rolling out, removes several functions from the Android recovery menu. After the update is applied to phones such as the S25 and Fold 7, long-standing features, such as the ability to wipe the device’s cache partition or install updates via Android Debug Bridge (ADB), disappear.