Hackaday has been online in some form or another since 2004, which for the Internet, makes us pretty damn old. But while that makes us one of the oldest surviving web resources for hacker types, we’ve got nothing on 2600 — they’ve been publishing their quarterly zine since 1984.
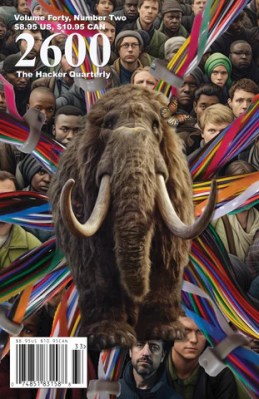
While the physical magazine can still be found on store shelves, the iconic publication expanded into digital distribution some time ago, thanks largely to the Kindle’s Newsstand service. Unfortunately, that meant Amazon’s recent decision to shutter Newsstand threatened to deprive 2600 of a sizable chunk of their income. So what would any group of hackers do? They took matters into their own hands and spun-up their own digital distribution system.
As of today you’re able to subscribe to the digital version of 2600 in DRM-free PDF or EPUB formats, directly from the magazine’s official website. Which one you pick largely depends on how you want to read it: those looking for the highest fidelity experience should go with PDF, as it features an identical layout to the physical magazine, while those who are more concerned with how the content looks on their reader of choice would perhaps be better served by the flexibility of EPUB. After signing up you can download the current Summer issue immediately, with future issues hitting your inbox automatically. Load it onto your home-built Open Book, and you can really stick it to the establishment.
While the ending of this story seems to be a happy one, we can’t help but see it as a cautionary tale. How many other magazines would have the means and experience to offer up their own digital subscriptions? Or for that matter, how many could boast readers savvy enough to utilize it? The reality is many publications will be injured by Amazon’s decision, some mortally so. That’s a lot of power to be put into the hands of just one company, no matter how quick the shipping is.