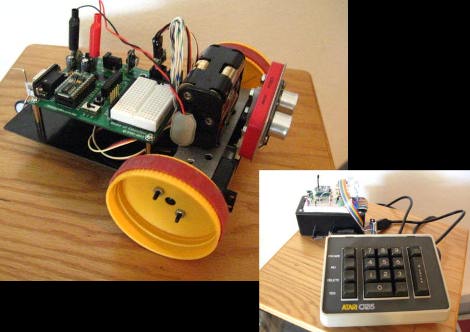
[PJ Allen] has been working on a little robot which he calls Cypherbot. The control circuitry is quite familiar; a Board of Education which features the Basic Stamp 2 microcontroller. This is an older and slower microprocessor, but it works quite well for this application since there’s no need for speed or heavy number crunching. The wheels of the bot are made out of plastic lids (we’re thinking peanut butter jars) with rubber bands for traction that are each driven by a servo motor. The third wheel is tiny and swivels as needed.
The front of the bot has a PING ultrasonic sensor mounted on a servo motor which lets the bot scan back and forth for a wider obstacle avoidance angle. In addition to the autonomous mode there’s an Xbee remote control. [PJ] picked up an Atari keyboard and is using that as the user input. Check out the little guy driving around the house in the video after the break.
Continue reading “Cypherbot Uses Older UC And Retro-controller”