EuroPython is a community-run developer conference, which began back in Belgium in 2002. In 2019, it’s happening in Basel, Switzerland from July 8 to 14, and there’s a special surprise in store for attendees this year. Conference attendees with be provided with a PewPew console for their hacking pleasure!
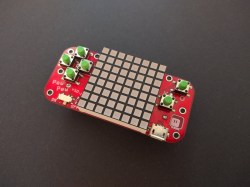
We’ve featured the project before on these hallowed pages; the earlier PewPew Featherwing console was a finalist in the 2017 Hackaday Prize Best Product Competition. At EuroPython, attendees will get to tinker with a special conference edition, which is the latest version of a long line of development versions. It runs the same microcontroller – ATSAMD21E18A – as the Adafruit Trinket M0, and is programmable with CircuitPython. The conference edition comes with a large 60 mm x 60 mm LED matrix, as well as an orange PCB with blue buttons to match the color scheme of the event.
We wager that conference attendees will enjoy hacking on the handheld console, and it makes a great platform for anyone who is new to embedded development with the Python language. Similar to badges, it makes a great pack-in for patrons, and the conference should be all the more enjoyable for it!