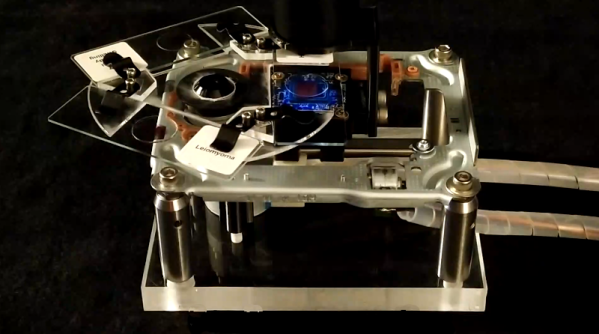
When you think of high-throughput ptychographic cytometry (wait, you do think about high throughput ptychographic cytometry, right?) does it bring to mind something you can hack together from an old Blu-ray player, an Arduino, and, er, some blood? Apparently so for [Shaowei Jiang] and some of his buddies in this ACS Sensors Article.
For those of you who haven’t had a paper accepted by the American Chemical Society, we should probably clarify things a bit. Ptychography is a computational method of microscopic imaging, and cytometry has to do with measuring the characteristics of cells. Obviously.
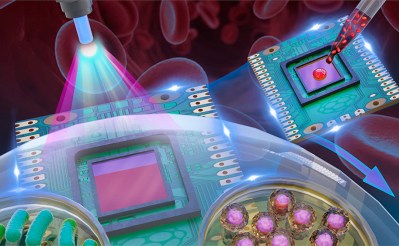
Anyway, if you shoot a laser through a sample, it diffracts. If you then move the sample slightly, the diffraction pattern shifts. If you capture the diffraction pattern in each position with a CCD sensor, you can reconstruct the shape of the sample using breathtaking amounts of math.
One hitch – the CCD sensor needs a bunch of tiny lenses, and by tiny we mean six to eight microns. Red blood cells are just that size, and they’re lens shaped. So the researcher puts a drop of their own blood on the surface of the CCD and covers it with a bit of polyvinyl film, leaving a bit of CCD bloodless for reference. There’s an absolutely wild video of it in action here.
Don’t have a Blu-ray player handy? We’ve recently covered a promising attempt at building a homebrew scanning electron microscope which might be more your speed. It doesn’t even require any bodily fluids.
[Thanks jhart99]