[youtube=http://www.youtube.com/watch?v=vsk6dJr4wps]
[Quethe] implanted an RFID chip into his hand so that he can access his handgun safe without having to fumble around for keys or buttons. He’s also planning to do more with the chip, including installing readers so he can access his car without keys. [Quethe] claims that inserting the chip hurts less than drawing blood. From the video he’s apparently using livestock grade equipment for the injection. While we applaud his ingenuity, we’re not sure that the convenience of easier access to guns and cars is actually worth the trouble of putting a chip in your body.
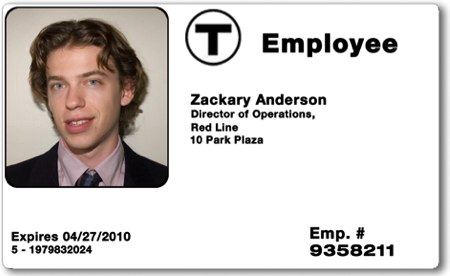
We’ve covered quite a a few hackers that have chosen to chip themselves in the past. [Mikey Sklar] did it back in 2005 after constructing a pair of pants to block the signal. [Amal Graafstra] ended up writing RFID Toys after implanting himself. [Larry Pesce] from the PaulDotCom podcast had his chip cloned on stage by [Major Malfunction] at ShmooCon. [Annalee Newitz] had her chip cloned by [Jonathan Westhues] while covering RFID hacking for Wired. It’s interesting to see the practice of DIY RFID chipping gaining traction, and, thankfully, all of the people just listed understand that it’s not a form of security.
[via Boing Boing]