Here’s an interesting kit put together just to help you work on your SMD soldering skills. It’s got 49 SMD LEDs on the front with a programming header and switch jumper. The back has an ATtiny26L and a coin cell. At only 3V, power management is essential; all of the example programs are only addressing one LED at a time (imperceptible to the human eye). If you turn on too many LEDs at the same time, the voltage drop could cause the AVR to reset. Included example programs are a scrolling marque, bouncing balls, and Conway’s game of life. SparkFun has tutorials for regular SMD soldering and using a reflow skillet. The video below shows the kit builder attaching just one LED using the heat and slide method.
Day: August 24, 2008
Improved Jog Wheel
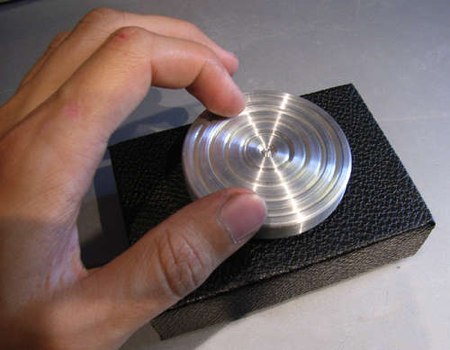
Taking a cue from the jog wheel we posted last week, [42ndOddity] has built an improved version. The design is based around a solid state rotary encoder instead of an optical encoder. The rotary encoder is far easier to attach and position properly. The knob is milled from scrap aluminum-it was a copier foot. To make the motion smooth, it’s sitting in a bearing from the same copier.
Rebooting The Magic SysRq Way

[Cory Wright] shares a tip on how to reboot a system with a failed hard drive remotely. The magic SysRq key is a linux kernel feature that lets you perform a number of interesting operations. If you’re working on a remote system where the disk has failed, you won’t have access to the reboot or shutdown commands. You can issue keystrokes to the magic SysRq device in /proc though, so you can send a hard reboot directly to the kernel with no disk access required.
The Wikipedia entry includes a handy tip on how to properly restart a otherwise frozen machine. It should save you from having to fsck the next time around.
[photo: Joshua Davis]
Subway Hacker Speaks
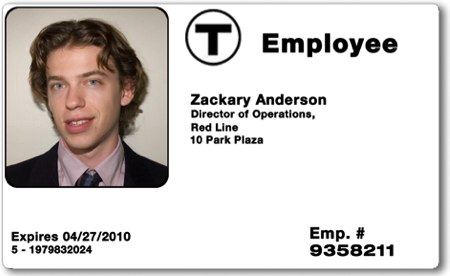
Popular Mechanics has an interview with [Zach Anderson], one of the MIT hackers that was temporarily gagged by the MBTA. The interview is essentially a timeline of the events that led up to the Defcon talk cancellation. [Zach] pointed out a great article by The Tech that covers the vulnerabilities. The mag stripe cards can be easily cloned. The students we’re also able to increase the value of the card by brute forcing the checksum. There are only 64 possible checksum values, so they made a card for each one. It’s not graceful, but it works. The card values aren’t encrypted and there isn’t an auditing system to check what values should be on the card either. The RFID cards use Mifare classic, which we know is broken. It was NXP, Mifare’s manufacturer, that tipped off the MBTA on the actual presentation.
Autonomous Paintball Sentry Gun

[Alan] pointed out this great commercial paintball sentry gun. The gun has a low power motherboard running Ubuntu connected to a firewire camera. Two high torque motors control the pan and tilt of a Tippman 98 custom. The control box allows for easy setup. You can change the sensitivity, color tracking, and firing modes. It also has a remote kill switch. All around a nice looking machine, but at $3K we doubt many of you will be buying one. Beta test video embedded after the break.










