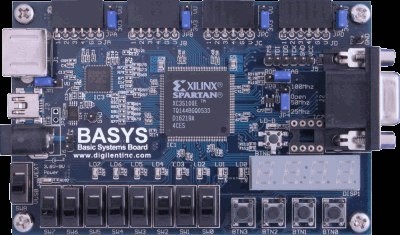
One of the more novel talks we saw at Defcon was [Zac Franken] presenting on access control systems. He covered several different types, but the real fun was his live demo of bypassing a hand geometry scanners like the one pictured above. With the help of two assistants, 4 pounds of chromatic dental alginate, and 5 liters of water, he made a mold of his hand. The box he placed his hand in had markings to show where the pegs on the scanner are located. After 2 minutes he could remove his hand from the cavity. They then filled the mold with vinylpolysiloxane, making sure to remove all bubbles. 20 minutes later the hand was solid and passed the scanner’s test. This may not be a completely practical attack, but it does defeat the overall idea of biometrics; biometrics are built on the assumption that every person is unique and can’t have their features reproduced.
[Zac] also showed an interesting magnetic card spoofer that emulated all three tracks using coils of magnet wire. We hope to see more about that in the future.
[photo: morgan.davis]