Back in the 90s, the console wars were in full swing. Nintendo vs Sega was an epic showdown at first, but when Nintendo seemed sure to clench the victory Sony came out of nowhere with the PlayStation. While these were the most popular consoles at the time, there were a few others around that are largely forgotten by history even if they were revolutionary in some ways. An example is the Pippin, a console made by Apple, which until now has been unable to run any software not signed by Apple.
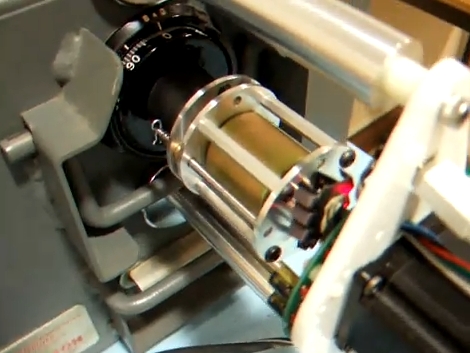
The Pippin was Apple’s only foray into gaming consoles, but it did much more than that and included a primitive social networking system as well as the ability to run Apple’s Macintosh operating system. The idea was to be a full media center of sorts, and the software that it would run would be loaded from the CD-ROM at each boot. [Blitter] has finally cracked this computer, allowing it to run custom software, by creating an authentication file which is placed on the CD to tell the Pippin that it is “approved” by Apple.
The build log goes into incredible detail on the way these machines operated, and if you have a Pippin still sitting around it might be time to grab it out of the box and start customizing it in the way you probably always wanted to. For those interested in other obscure Apple products, take a look at this build which brings modern WiFi to the Apple Newton, their early PDA.
Continue reading “90s Apple Computer Finally Runs Unsigned Code”