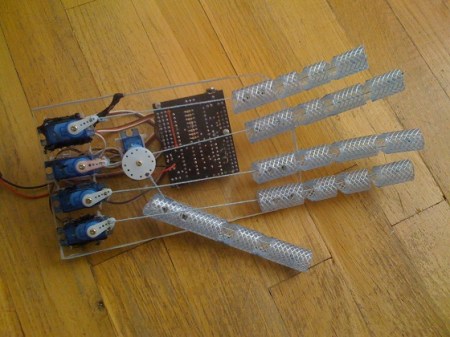
[Sebastian] is trying to improve the responsiveness of an electric keyboard. He was unsatisfied with the lack of adequate sensitivity to keystroke. The first step in his process was to measure how fast the quickest keystroke actually is. By setting up an LED and phototransistor and taking some measurements he found that sampling at 1 kHz would be more than adequate.
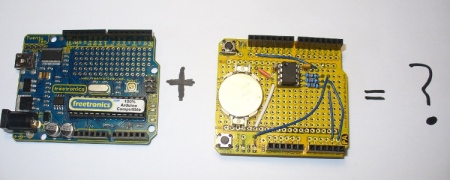
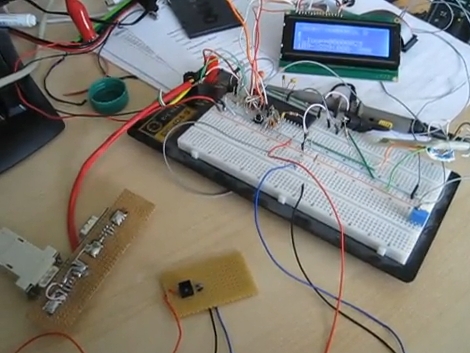
With initial testing complete he ordered some CNY70 transmissive/reflective light sensors that can be place below the keys. He measures the sensor with the ADC on an ATmega16 microcontroller. Running at 16 MHz he can sample each of the eight analog-to-digital converter channels at 1202 Hz. After doing a bunch of math he put together some lookup tables that are used to translate the ADC data into midi signals. We’ve embedded a video of one sensor controlling the midi program PianoTeq. [Sebastian] also sent us a schematic of one node in the sensor network (see it after the break).
When everything is said and done he plans to use eleven ATmega16 microcontrollers to address the 88 keys, with an additional microcontroller to act as the master using a two-wire interface for communications.
Update: [Sebastian] put up a webpage with a fairly verbose description. Reading it straight from the source really clears up a lot of questions.