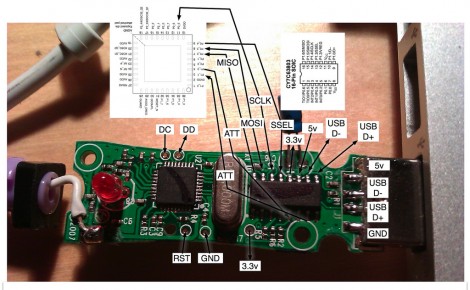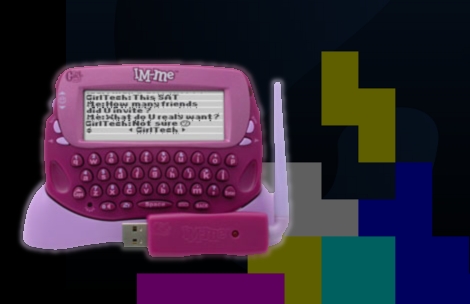
[Emmanuel Roussel] is coding a version of Tetris for the IM-ME. Before you get too excited, he hasn’t actually written the game yet, but instead started with the familiar theme music. The IM-ME has a piezo speak on board so it’s just a question of frequency and duration. [Emmanuel] developed an Open Office spread sheet that calculates each note’s frequency and the timer value needed to produce it. He then created a data type that stores a note and its duration and used an array of those structures to store the song. If you’ve ever wondered how to cleanly code music this is a wonderful example to learn from because right now the code doesn’t have anything other than that code to get in the way.
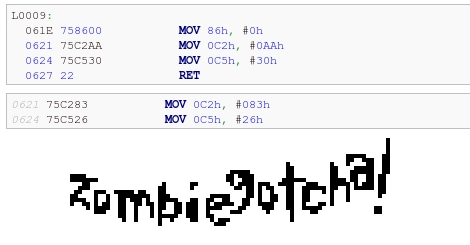
The ground work for this was established in the other hacks we’ve seen. Now we’re left wondering who will finish coding their game first. Will it be [Emmanuel’s] Tetris or [Travis’] Zombie Gotcha?