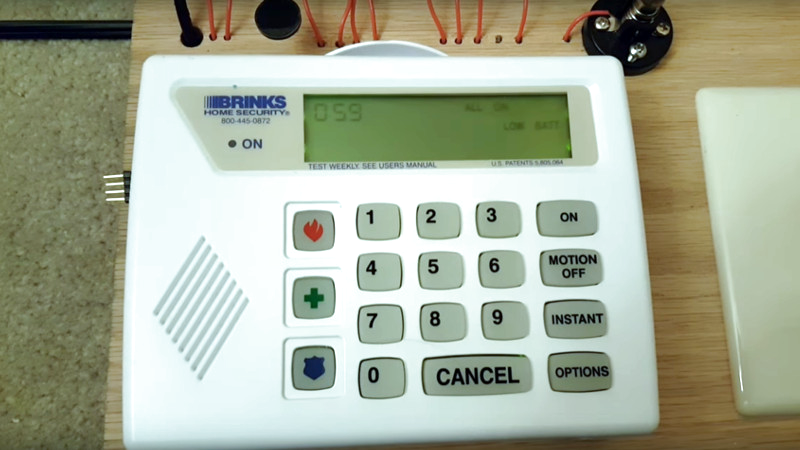
When a tip comes in and the tipster feels they have to reassure us that despite appearances their subject is not facilitating crime, it certainly gets our attention. [Flam2006] has a Brinks home security system which can only be configured using a special device only available to installers, and though they managed to secure one through an eBay sale they went to the trouble of reverse engineering its protocol and writing a software emulator in Python. When an owner hacks their own security system to gain full control of something they own, that’s right up our street.
The communication is via an RS485 serial line, and follows a packetised structure with binary rather than ASCII data. There is an almost plug-and-play system for identifying devices connected to a controller, though it is restricted to those devices which the controller already knows about. There is a video of the official method of programming the controller, as well as one of the software in action. We’ve posted them below the break for your delectation.
The ability to perform these tasks on your own property is an important right that has at times been placed under threat by legislation such as the DMCA. We’ve touched upon it countless times, but probably the most high-profile example that we and the wider media have covered are those stories concerning the parts lockdown on John Deere tractors.















HA! I have that security panel AND I’ve already started tapping into the sensors around the house! Oh [Flam2006], you’ve made me a very happy hacker today!
Help I’ve fallen and I can’t get up!
If you like this you will love Konnected which does this for you. Website is konnected.io
Wow! This would have been right at home if authored/blogged by the venerable Samy Kamkar or Michael Ossmann. Thx for posting!
I’ve never had an alarm system, so I’m curious what the benefit would be?
The main benefit of an alarm is that it will tell you that someone is in your house and two steps away from shooting then robbing you.
The whole idea of “digital rights” is to ensure people never really own their stuff any more… good to see articles/projects like this (even though I don’t own this particular system)!
I’ve never had an alarm system, so I’m curious what the benefit would be?
The binary data is probably encoded in ASN.1, which is a standard data protocol for both binary data and plain-text data. While the binary form is unreadable for humans, they’re actually quite easy for computers to parse. The biggest challenge is that there aren’t that many good, open-source ASN.1 tools available. Which is weird as ASN.1 is part of the Internet backbone…
There’s a reason security systems shouldn’t be tampered with, other than by trained engineers! If u start messing with the programming not knowing exactly what you are doing & why, then have an issue or burglary & need to call out the alarm company for maintenance or repair, you will then get a big bill for repairs/rectification!
Not to mention it will kill off any kind of insurance benefit you would get for having an alarm system. A tampered alarm system is compromised in their view. I like the hack and kudos to them for sharing tho :) Just wanted to throw that caution in there.
You can rip out that proprietary Brinks/ADT/whatever and replace it with something mainstream (and better) for a few hundred dollars and get on with life. It’s really no big deal.
No there’s not. Alarms can be used by you or anyone. They aren’t complicated. No alarm company sends a professional, college-certified engineer to change your alarm. They send a guy specialized at pulling wires and selling you parts. There is almost no special skill needed now that most systems are wireless. And the wired systems, if they are already wired back to the panel, are extremely easy to use and program as well.
I’m a security technician that has been in the industry for 25 years. I’ve programmed Ademco, FBI, DSC ,DMP, Napco Caddox and Scantronic security systems. The program belongs to the customer since it is configured to specifically work with their system. Once a customer gets into the program, they can screw it up if they don’t entirely know what they are doing. It is not wise to do this with a currently monitored system by a security company. Once you start adding devices, zones or just start changing info, you run the risk of central station not knowing what an identifying code is to a zone that was added after the system was registered with them. Or just maybe you changed something to do with 24 hr test signals. All the signals that the system will send pertaining to the installation site are registered with the central station through the Dealer a.k.a. the installing company. So when the hacked system starts to report a signal to central station that is not registered with them, they will log a NCF which is No Code on File. Changing the 24 hour test time can cause unnecessary phone calls to the residence because the receiver at central station knows when it’s supposed to receive the test time from the panel. So unless you make your security company aware of the changes you made, they may not get dispatched on by central station. In some cases the Security Company may look at it as a breach of warranty for the system. This of course depends on how long the warranty period is for. In other words, speak with the installers or others at the company who put your system in. Trying to program the system yourself could mean a non working system.
Yep. Not all systems are monitored though. Brinks has been known to remotely disable systems when monitoring service is canceled, and now the owners of these systems have a way to re-enable them without signing another service contract.
See also the disclaimer in my Github repository.
The equipment they sell is fairly cheap, it’s the service that makes the money for them. Pretty much like any other contract device (cell phone, cable box…). Now, if you could have a phone app, that monitors your system, and send you alerts, instead of their service… An audio alarm is little guaranty that someone is going to be there, or motivated enough to call the police for you. Personally, video security is a better deterrent, when the cameras are placed in clear view. Once a thief or vandal spots the cameras, they usually are on their best behavior, and find a less risky target. The only ones that ignore the cameras, are people who know there is something worth the added risk, or have a personal interest in victimizing you. Don’t flash your cash, don’t screw people over, and you have little to worry about.
Ccrv alone is NOT a solutiin, crims that see there are cameras will either spray black paint over the lrnss or wear balaclavas to cover their idrntitj or even desroy the cameras. Used in cinjunction with a professiinally monitored alarm and using cameras or rven new Pir cams to verify an actual human intruder in real time. NOT a belejver in self monitoring( using your smarr phone To minitor your alarms/ cameras) without back up from professional minitoring centre is false and foo. Ish practise. What if on train to work or in meeting at work unable to trcive signal whrn someonr is jnside your house, thieving or bashing your partneg.? ??
Our house got broken into two times when I was a kid, both times while we were all out of the house. We had a super-loud siren system, but nothing more. Built it ourselves out of parts/modules from Radio Shack — a fun father-son weekend, honestly.
I disagree about the effectiveness of a siren.
In 2/2 cases, a freaking loud siren encouraged thieves to vacate the premises before the police show up. One time, the fleeing perpetrator (actually a neighbor, schizophrenic, many troubles, long story) dropped everything he had while fleeing.
Our neighbors _did_ call the cops. And we did for them at least once that I can remember. And the police did show up, but always too late of course. As stated above, a blaring siren encourages evacuation.
Good times.
Anyway, I don’t want to know that there’s a robber breaking into my house as much as I want the robber to know that we (all) know.
A slight correction here: it does use ASCII data in some places, including for the text that appears on the programmer screen.
your software does not install correctly….can you explain you installation a bit clearer
Thanks for publishing this. If you want a system monitored by a 3rd party, it is probably best to leave it alone. However, if you want to monitor it yourself, add and customize features: go for it! I did something similar for the Honeywell Vista series alarms (very commonly installed in my area). My code and interfaces circuits are on github here (https://github.com/TomVickers/Arduino2keypad) and here (https://github.com/TomVickers/RPIalarm). The Arduino2keypad project provides an serial to keybus protocol translator, which is useful for interfacing with the Honeywell 6160 style keypads. For my setup, I replaced the Honeywell alarm board with a raspberry pi.
I have this system in the house we just bought. Previous owner disconitued service and it worked locally for a few weeks and now is disabled. How can I easily reprogram to work again locally