Plotters aren’t as common as they once were. Today, many printers can get high enough resolution with dots that drawing things with a pen isn’t as necessary as it once was. But certainly you’ve at least seen or heard of machines that would draw graphics using a pen. Most of them were conceptually like a 3D printer with a pen instead of a hotend and no real Z-axis. But as [biosrhythm] reminds us, some plotters were suspiciously like typewriters fitted with pens.
Instead of type bars, type balls, or daisy wheels, machines like the Panasonic Penwriter used a pen to draw your text on the page, as you can see in the video below. Some models had direct computer control via a serial port, if you wanted to plot using software. At least one model included a white pen so you could cover up any mistakes.
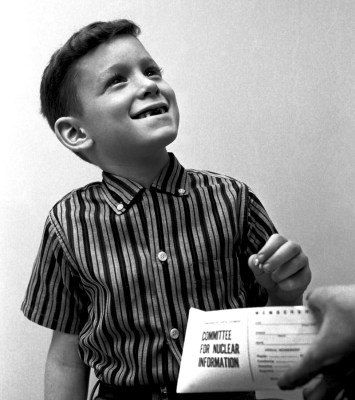
If you didn’t have a computer, the machine had its own way to input data for graphs. How did that work? Read for yourself.