[Robert’s Retro] is one of those great YouTube channels that shows us the ins and outs of old and obscure computers. [Robert] likes going a step beyond the traditional teardown though, repairing and upgrading these old machines. His latest project involves giving the ZEOS Pocket PC a fully-functional serial port.
If you’re unfamiliar with the ZEOS Pocket PC, you might know it as the Tidalwave PS-1000—it’s a pretty straightforward clone. Originally, these machines could be had with a proprietary serial adapter to enable them to interface with external peripherals. However, like most obscure cables and connectors from three decades ago, they’re virtually unobtainable today.
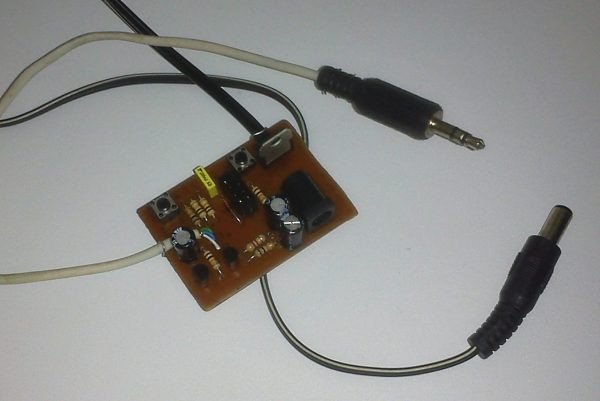
To solve this problem, [Robert] decided to hack in a traditional DE-9 connector instead. Commonly referred to as the DB-9, this is the most common serial port design used on IBM PCs and compatibles. Getting the larger port into the compact PC required some careful hacking of the case, as well as delicate soldering to hook up the pins to the right signals on the tightly-packed motherboard. This video does involve cutting some vintage plastic, but overall it’s a very neat mod that is handled with due respect and care.
This isn’t the first time we’ve seen him upgrade a classic portable computer, either.
Continue reading “Ancient Pocket Computer Gets A Serious Serial Upgrade”