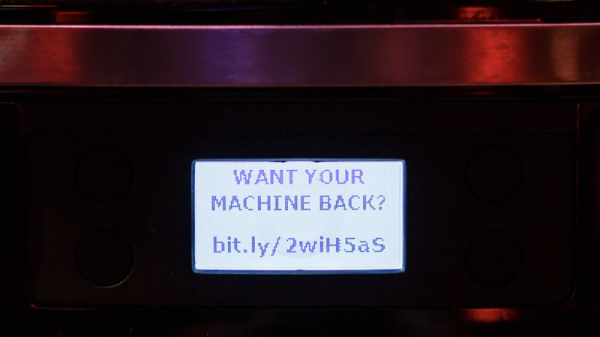
You wake up on a Sunday, roll out of bed, and make your way to the centerpiece of your morning, the magical device that helps you start your day: the coffee machine. You open the companion app, because everything has an app in 2020, and select a large latte with extra froth. As you switch open a browser to check Hackaday, the machine beeps. Then the built-in grinder cranks up to 100, the milk frother begins to whir, and the machine starts spraying water. Frantic, you look at the display for an error code and instead see a message instructing you to send $75 to a bitcoin wallet, lest your $300 machine become a doorstop.
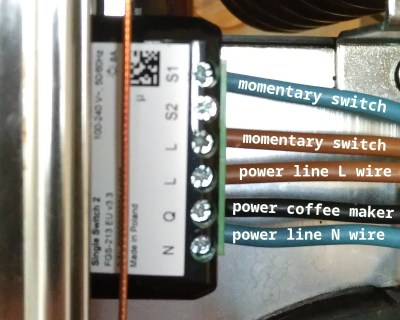
Outlandish though it may seem, this has become quite a real possibility, as [Martin Hron] at the Avast Threat Labs demonstrates. In fact, he could probably make your modern macchiato machine do this without setting foot in your house (so long as it comes with a built-in ESP8266, like his did).
Building on others’ work that identified the simple commands that control the machine over it’s WiFi connection (nothing says “brew me a nice cup o’ joe” like 0x37), [Martin] reverse-engineered the Smarter Coffee companion app to extract and reverse engineer its firmware. He was actually able to find the entire firmware image packaged within the app- relatively uncommon in the world of Over-The-Air (OTA) updates, but convenient in this case. Using Interactive Disassembler (IDA) to sift through the firmware’s inner workings, he identified the functions that handle all basic operations, including displaying images on the screen, controlling the heating elements, and of course, beeping. From there, he modified the stock firmware image to include some malicious commands and ran an OTA update.
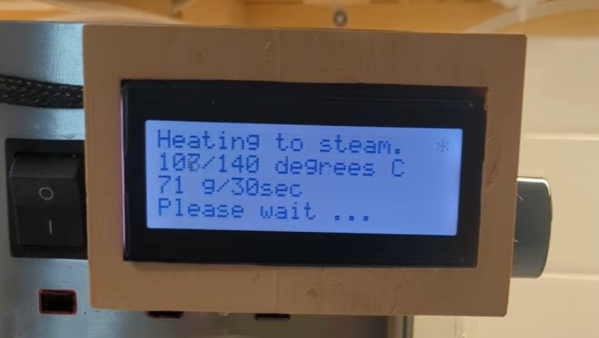
The mind-boggling part here is that not only was the firmware transmitted as unencrypted plaintext over unsecured WiFi, but the machine didn’t even require a user to confirm the update with a button press. With one quick reboot, the trap was set. The machine operated normally, while waiting for “Order 66,” causing it to turn all the heating elements on, spool up the built-in grinder, and beep. Constantly.
While a broken coffee machine seems relatively innocuous, there are some pretty significant lapses in hardware/firmware security here that, while avoidable, almost seem unnecessary in the first place. It makes us wonder- why does Mr. Coffee need a smartphone in the first place?
Continue reading “WiFi Hacking Mr. Coffee” →