For a workshop at the ECAL University of Art and Design in Switzerland, students were asked to come up with new unorthodox ways to capture video using a GoPro camera. The results are pretty awesome.
Lead by the Dutch designer [Roel Wouters], students in the Media & Interaction Design program worked together with Industrial Design students to create these fascinating camera rigs. From “the eye”, a water based stabilizing ball, to a silly bobble hat can be spun around the user, the results are super fun and unique to watch. The workshop was one week long and produced five different camera rigs as featured in the following video.
Continue reading “Unorthodox GoPro Camera Rigs Produce Unreal Videos”








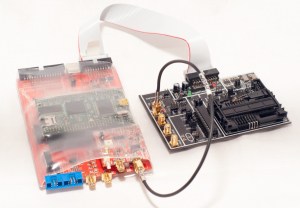
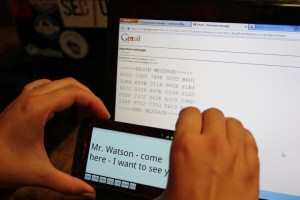
 In honor of DEFCON, this week we’re looking at some cryptography and reverse engineering projects over at Hackaday.io
In honor of DEFCON, this week we’re looking at some cryptography and reverse engineering projects over at Hackaday.io 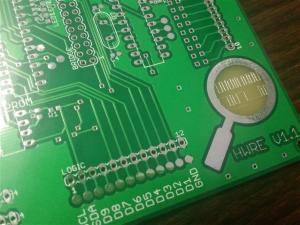


 It’s Friday morning and time for another round of Astronaut Or Astronot, the little lottery thing where we’re giving away
It’s Friday morning and time for another round of Astronaut Or Astronot, the little lottery thing where we’re giving away