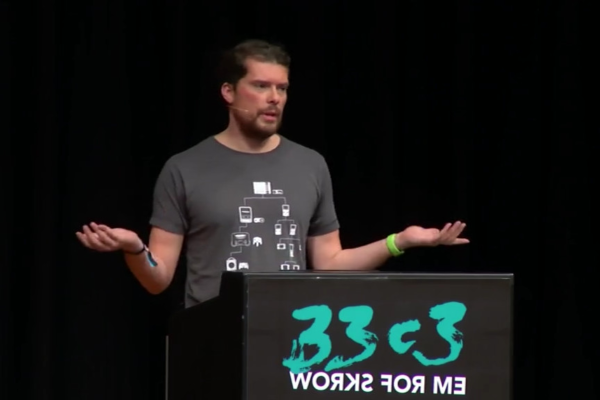
The 39th annual Chaos Communication Congress (39C3) is underway, and it kicked off with a talk that will resonate deeply with folks in the Hackaday universe. [Kliment] gave an impassioned invitation for everyone to start making hardware based on his experience both in the industry and in giving an intro-to-surface-mount workshop to maybe thousands of hackers over the years.
His main points are that the old “hardware is hard” cliche is overdone. Of course, working on a complicated high-reliability medical device isn’t child’s play, but that’s not where you start off. And getting started in hardware design and hobby-scale manufacture has never been easier or cheaper, and the open-source tooling gives you a foot in the door.
He tells the story of an attendee at a workshop who said “I kept waiting for the hard part to come, but then I was finished.” Starting off with the right small-scale projects, learning a few techniques, and ramping up skills built on skills is the way to go. ([Kliment] is a big proponent of hand-placed hot-plate reflow soldering, and we concur.)
This is the talk that you want to show to your software friends who are hardware-curious. It’s also a plea for more experimentation, more prototyping, more hacking, and simply more people in the hardware / DIY electronics scene. Here at Hackaday, it’s maybe preaching to the choir, but sometimes it’s just nice to hear saying it all out loud.