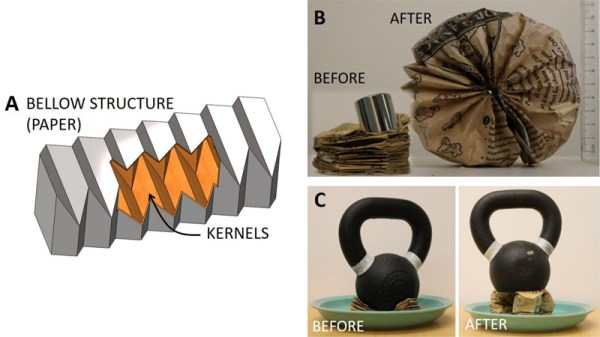
Popcorn! Light and fluffy, it is a fantastically flexible snack. We can have them plain, create a savory snack with some salt and butter, or cover with caramel if you have a sweet tooth. Now Cornell University showed us one more way to enjoy popcorn: use their popping action as the mechanical force in a robot actuator.
It may be unorthodox at first glance, but it makes a lot of sense. We pop corn by heating its water until it turns into steam triggering a rapid expansion of volume. It is not terribly different from our engines burning an air-fuel mixture to create a rapid expansion of volume. Or using heat energy to boil water and trigger its expansion to steam. So a kernel of popcorn can be used as a small, simple, self-contained engine for turning heat energy into mechanical power.
Obviously it would be a single-use mechanism, but that’s perfectly palatable for the right niche. Single-use is a lot easier to swallow when popcorn is so cheap, and also biodegradable resulting in minimal residue. The research paper demonstrated three recipes to harness popping corn’s mechanical energy, but that is hardly an exhaustive list. There’s an open invitation to brainstorm other creations to add to the menu.
Of course, if you prefer candy over popcorn, you could build a robot actuator out of licorice instead.
Either way, the robot uprising will be delicious.
[via IEEE Spectrum]
Continue reading “Hold The Salt And Butter, This Popcorn Is For A Robot”