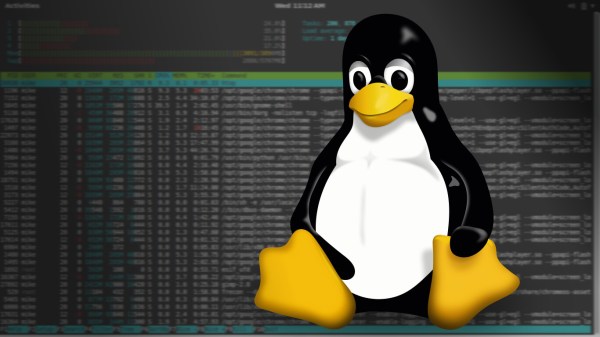
The title of this post says it all: GoTTY is a program that lets you share Linux terminal applications into a web browser. It is a simple web server written in Go that runs a non-GUI program and can push it out a socket in such a way that a browser can display it and, optionally, let the user interact with it.
With the emphasis on security these days, that ought to alarm you. After all, why would you want a shell running in a browser? Hang on, though. While that is possible — and not always undesirable — the real value to this technique is to run a specific command line program in a browser window. Here’s a use case: You want users to remotely monitor a system using top (or htop, if you are fancy). But you don’t want users logging into the system nor do you want to require them to have ssh clients. You don’t want to install monitoring tools, just use what you already have.
If you could get the output from top to show up in a browser window — even if the users had no ability to input — that would be an easy solution. Granted, you could just run top in batch mode, collect the output, and write it somewhere that a web server could find it. Assuming you have a web server installed, of course. But then what if you did want some other features like taking command line options or having the option for (hopefully) authenticated users to interact with the software? Now that would be more complicated. With GoTTY, it is easy.