[easybakejake] figured out a way to fuse together an iPod speaker dock and a wireless Chromecast receiver. His method utilized a modified HDMI-to-VGA adapter. From the looks of it, apps like music for Google Play, Pandora, and Music All Access seem to able to be streamed through this device.
A few problems did come up with this project though when researching the functionality of this music hack. For one, there is little to no documentation since the tip came to us through a Reddit post. Another inconvenience had to do with supporting different monitor sizes. [easybakejake] confirmed in the comments of that post that he ran into an error where the input was not working; probably due to a resolution issue. Eventually, he got it working and dubbed the device the MusicBox. Now stick it on a roomba and get it to DJ a party (like this Parks and Recreation skit that follows after the break):
Continue reading “An IPod Dock Converted Into Chromecast Speakers”

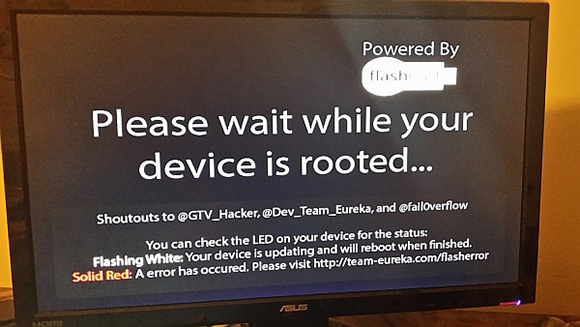

 With a simple $35 dongle that plugs right into your TV, it’s possible to enjoy your favorite TV shows, YouTube channels, and everything else Chromecast has to offer. Being a WiFi enabled device, it’s also possible to hijack a Chromecast, forcing your neighbors to watch
With a simple $35 dongle that plugs right into your TV, it’s possible to enjoy your favorite TV shows, YouTube channels, and everything else Chromecast has to offer. Being a WiFi enabled device, it’s also possible to hijack a Chromecast, forcing your neighbors to watch