[Rafael Scheel] a security consultant has found that hacking smart TVs takes nothing much more than an inexpensive DVB-T transmitter, The transmitter has to be in range of the target TV and some malicious signals. The hack works by exploiting hybrid broadcast broadband TV signals and widely known about bugs in web browsers commonly run on smart TVs, which seem run in the background almost all the time.
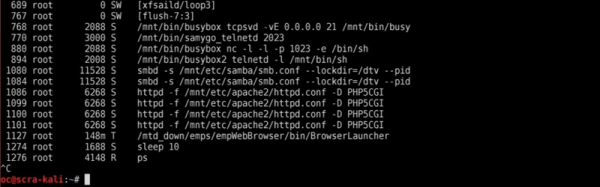
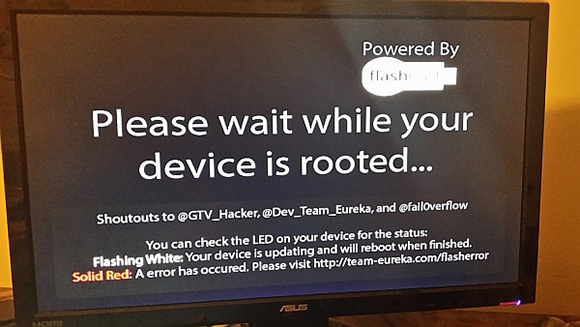
Scheel was commissioned by Cyber security company Oneconsult, to create the exploit which once deployed, gave full root privileges enabling the attacker to setup and SSH into the TV taking complete control of the device from anywhere in the world. Once exploited the rogue code is even unaffected by device reboots and factory resets.
Once a hacker has control over the TV of an end user, he can harm the user in a variety of ways, Among many others, the TV could be used to attack further devices in the home network or to spy on the user with the TV’s camera and microphone. – Rafael Scheel
Smart TV’s seem to be suffering from IoT security problems. Turning your TV into an all-seeing, all-hearing surveillance device reporting back to it’s master is straight out of 1984.
A video of a talk about the exploit along with all the details is embedded below.
Continue reading “Remotely Get Root On Most Smart TVs With Radio Signals”