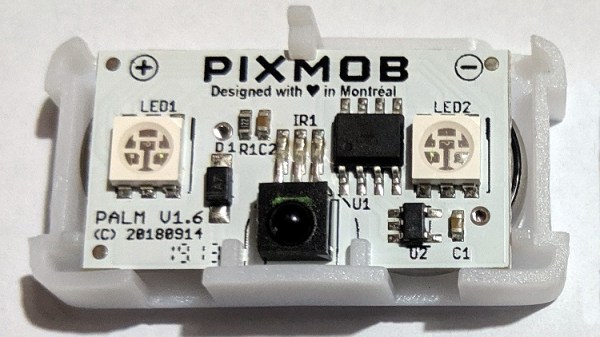
Over the last few years, it’s been increasingly common for concertgoers to be handed a light-up bracelet from PixMob that synchronizes with the others in the crowd to turn the entire audience into a music visualizer. They’re a clever way of enhancing the concert experience, but unfortunately, they don’t do anything once you leave the show. Or at least, that used to be the case.
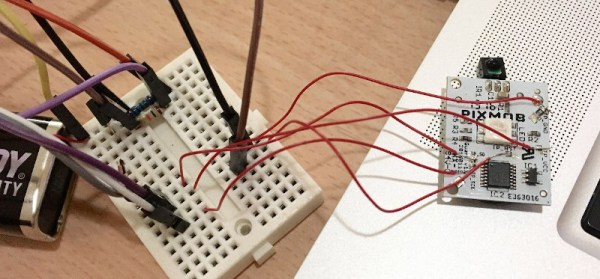
We’ve seen efforts to reverse engineer the IR (and occasionally radio) signals that drive these PixMob devices, but since we checked in last it seems like things have gotten a lot easier for the home gamer. [David Pride] has recently posted a brief write-up that shows how quickly and easily it is to get these devices fired up using nothing more exotic than an Arduino, an IR LED, and an audio sensor module.
 With the audio sensor module connected to the Arduino’s digital input and the IR LED wired to digital out, all you need to do is flash firmware to the board and start playing some beats. The source code [David] has provided is a a remixed version of what’s previously been published by [Carlos Ganoza], which, in this case, has been tweaked to make the lighting patterns less random.
With the audio sensor module connected to the Arduino’s digital input and the IR LED wired to digital out, all you need to do is flash firmware to the board and start playing some beats. The source code [David] has provided is a a remixed version of what’s previously been published by [Carlos Ganoza], which, in this case, has been tweaked to make the lighting patterns less random.
Presumably, this is to make the devices behave more like they do during an actual concert, but since nobody at Hackaday is cool enough to have seen a live musical performance in the last decade, we’re not really sure. All we can say is that the effect looks pretty sweet in the demo video.
Back in 2019, we saw a teardown of an early PixMob device, and by 2022, the efforts to reverse engineer their IR control protocol were well underway. We’re glad to see things have progressed to the point that you can piece together a transmitter from what’s in the parts bin, as it means at least some of these devices will have a lifespan longer than a single concert.