As home automation becomes more and more popular, hackers and security experts alike are turning their attention to these systems, to see just how (in)secure they are.
This week at DefCon, a pair of researchers demonstrated just how vulnerable home automation systems can be. Carrying out their research independently, [Kennedy] and [Rob Simon] came to the same conclusion – that manufacturers of this immature technology have barely spent any time or resources properly securing their wares.
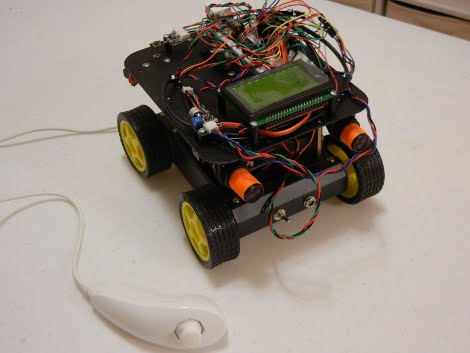
The researchers built tools that focus on the X10 line of home automation products, but they also looked at ZWave, another commonly used protocol for home automation communications. They found that ZWare-based devices encrypted their conversations, but that the initial key exchange was done in the open, allowing any interested 3rd party to intercept the keys and decrypt the communications.
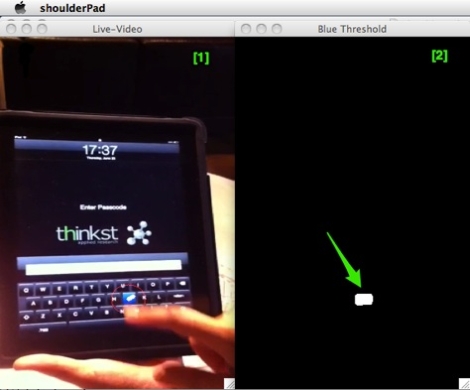
While you might initially assume that attacks are limited to the power lines within a single house, [Kennedy] says that the signals leak well beyond the confines of your home, and that he was able to intercept communications from 15 distinct systems in his neighborhood without leaving his house.