Rather than having users go through the inconvenience of having to punch in their current location, an increasing number of applications and websites use location services that can pin-point the current location of a user to within a certain number of meters or kilometers.
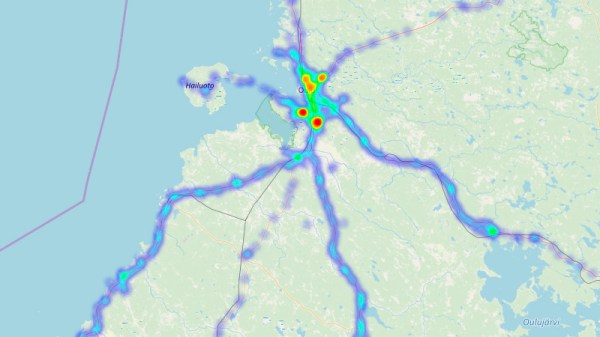
Unfortunately, [Evert Pot] found that with the demise of the Mozilla Location Service (MLS) in 2024, accuracy of the Linux Geoclue service had dropped to a resolution of about 25 km. Since a LAN tends to not move around a lot, this seemed like the perfect time to help Geoclue out with a local GPS server.
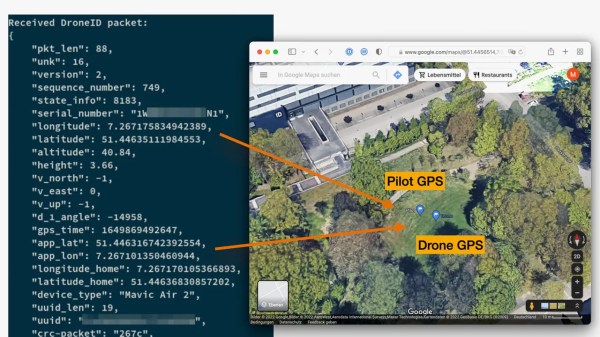
All that Geoclue looks for on the LAN is an mDNS service identifying as _nmea-0183._tcp that responds with the GPS coordinates as network packets containing an ASCII payload encoded using the NMEA 0183 standard. With this knowledge [Evert] was then able to quickly put together a Python-based server that simply blasts the static GPS coordinates of the LAN in question.
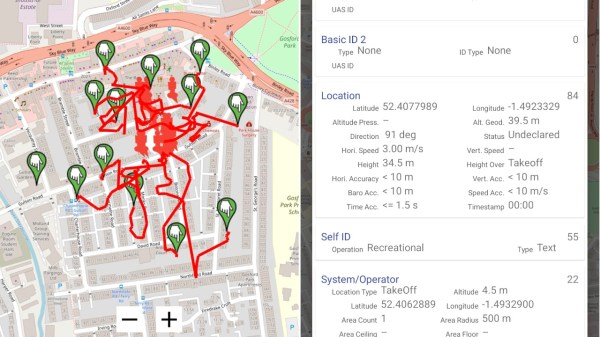
With the service running, Gnome Maps and Firefox with Google Maps both displayed the right location down to the house, as can be seen in the screenshots. With the same LAN service and a Mac system there was no such luck with Apple Maps unless Location Services was turned off, though presumably Apple uses its own equivalent to MLS.