If we’re talking about oxidized iron… probably nobody. If we’re talking about Rust the programming language, well, that might be a different story. Google agrees, and is working on bringing the language into Android. That’s not enough for [Paul Sanja], who has the first Redox OS smartphone.

Redox OS is a Unix-like operating system written entirely in Rust, and somehow we haven’t covered it until now. Unlike Asterinas, a project to recreate the Linux kernel in Rust, Redox has few pretensions of being anything but its own thing, and that’s great! On desktop, Redox has a working windowing system and many utilities, including a basic browser in the form of NetSurf.
It’s claims to be source-compatible with Linux and BSD programs, and partially POSIX compliant. A certain someone around here might want to try it as a daily driver. The header image is a desktop screenshot, because there’s more to see there and it fits our aspect ratio.
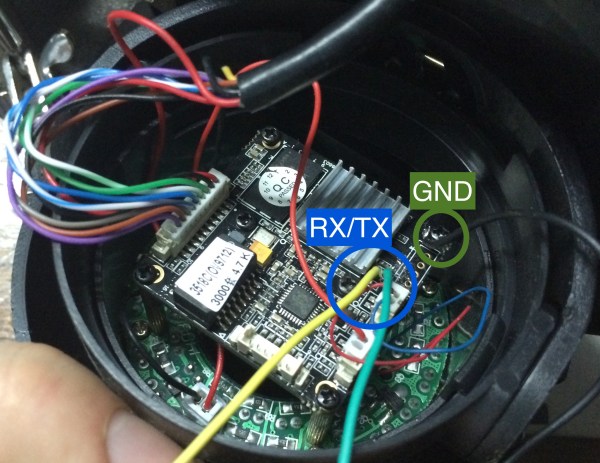
On smartphones, it… boots. Some smartphones, anyway. It’s actually a big first step. That booting is possible is actually thanks to the great work put in by the Postmarket OS team to get Uboot working on select android devices. That uboot loader doesn’t need to load the Linux-based Postmarket OS. It can be used for anything compatible. Like, say, Redox OS, as [Paul] shows us.
Of course, Redox OS has no drivers for the touchscreen or anything else, so at the moment that rusty smartphone can only boot to a login screen. But thanks to Rust, you can rest assured that login screen hasn’t got any memory leaks! Jokes aside, this is a great start and we’re hoping to see more.
Redox is a promising project on mobile or desktop, and its development seems a much better use of time and effort than fighting over Rust in the Linux kernel.