In a slight twist on the august pursuit of warwalking, [Mehdi] took a Raspberry Pi armed with a GPS, WiFi, and a Bluetooth sniffer around Bordeaux with him for six months and logged all the data he could find. The result isn’t entirely surprising, but it’s still a little bit creepy.
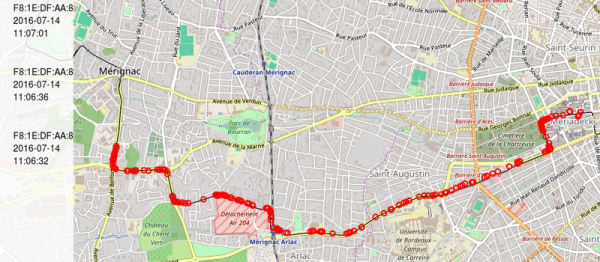
If your WiFi sends out probe requests for its home access points, [Mehdi] logged it. If your Bluetooth devices leak information about what they are, [Mehdi] logged it. In the end, he got nearly 30,000 WiFis logged, including 120,000 probes. Each reading is timestamped and geolocated, and [Mehdi] presents a few of the results from querying the resulting database.