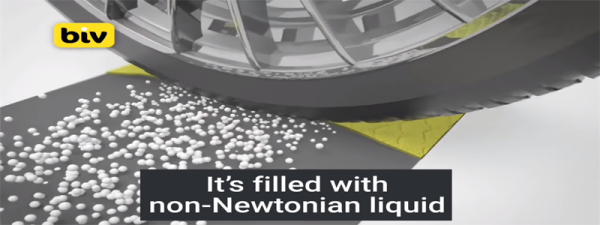
Like it or not speed bumps are an essential part of our road infrastructure especially in built-up places like near schools [Business Insider UK] reports non-Newtonian liquid filled speed bumps are being tested in Spain, Israel and Germany.
Traditional speed bumps do have their drawbacks; damage to the underside of low vehicles is common. While they should be uniform in dimensions, in practice they can vary significantly, making driving over unfamiliar bumps a bit unpredictable. This is all set to change with non-Newtonian bumps which are soft to drive over at slow speeds but for speeding drivers they harden up and act more like traditional bumps. This gives drivers following the letter of the law a better driving experience whilst still deterring speeding drivers..
Non-Newtonian materials are nothing new but we think this is a great way of purposing these type of materials. Roads are getting smart whether you like it or not. It’s time to embrace technology and improve our commutes. Continue reading “Smart Speed Bumps Slow Only Speeding Cars”