It’s desirable to have your Internet connection up at all times, particularly as it can take some time to get back online if you have a power interruption or similar. [Brink] had some issues with the power supply in their apartment, so they set about whipping up a backup power solution to keep their Verizon ONT fiber modem up and running in such events.
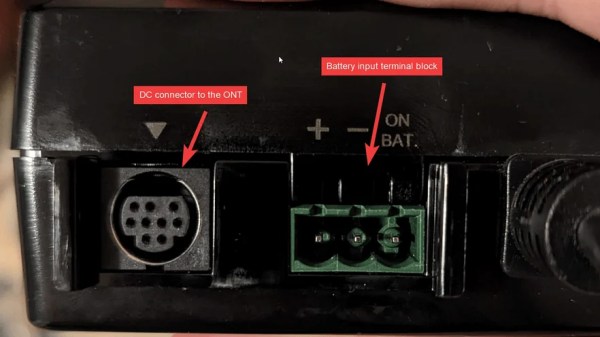
The I-211M-L modem is actually equipped to run on backup battery power, but by default, it will only keep phone service online. Data and television services are normally switched off when the mains supply goes out. Thankfully, a minor mod to the unit’s power cable shared by [mousehunt] enables it to keep data services online when running on backup power. Grounding a bunch of pins with a strip of foil is enough to do the job.
From there, it’s a simple matter of hooking up a stout 12 V battery to the modem via its backup power connector. [Brink] specified a nifty 12 V rechargeable lithium ion pack for the job, which is sold as a portable power unit for running LED strips. Some neat cabling to keep the battery charged later, and you’ve got a working UPS setup to keep the comms online.
Combined with a UPS to run the rest of your computers and networking equipment, this is a great solution to stay online during local power outages. We’ve featured some other great UPS hacks over the years, too, like these supercap UPSs for special cases. If you’ve got your own nifty power hacks, don’t hesitate to drop us a line!