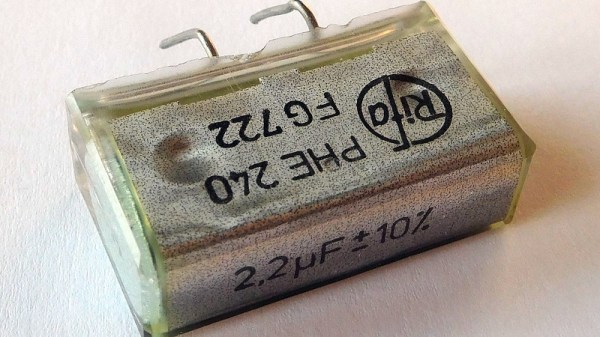
Anyone who works with older electronic equipment will before long learn to spot Rifa capacitors, a distinctive yellow-translucent component often used in mains filters, that is notorious for failures. It’s commonly thought to be due to their absorbing water, but based upon [Jerry Walker]’s long experience, he’s not so sure about that. Thus he’s taken a large stock of the parts and subjected them to tests in order to get to the bottom of the Rifa question once and for all.
What he was able to gather both from the parts he removed from older equipment and by applying AC and DC voltages to test capacitors, was that those which had been used in DC applications had a much lower likelihood of exhibiting precursors to failure, and also a much longer time before failure when connected to AC mains.
Indeed, it’s only at the end of the video that he reveals one of the parts in front of him is an ex-DC part that’s been hooked up to the mains all the time without blowing up. It’s likely then that these capacitors didn’t perform tot heir spec only when used in AC applications. He still recommends replacing them wherever they are found and we’d completely agree with him, but it’s fascinating to have some light shed on these notorious parts.