This series of monthly teardowns was started in early 2018 as an experiment, and since you fine folks keep reading them, I keep making them. But in truth, finding a new and interesting gadget every month can sometimes be a chore. Which is why I’m always so thankful when a reader actually sends something in that they’d like to see taken apart, as it absolves me from having to make the decision myself. Of course it also means I can’t be blamed if you don’t like it, so keep that in mind as well.
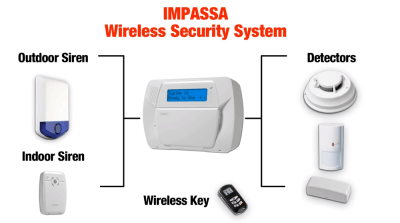
Coming our way from the tropical paradise of Eastern Pennsylvania, this month’s subject is an ADT branded Impassa SCW9057G-433 alarm system that was apparently pulled off the wall when our kind patron was moving house. As you might have guessed from the model number, this unit uses 433 MHz to communicate with various sensors and devices throughout the home, and also includes a 3G cellular connection that allows it to contact the alarm monitoring service even if the phone line has been cut.
From how many of these are on eBay, and the research I’ve done on some home alarm system forums, it appears that you can actually pick one of these up on the second-hand market and spin your own whole-house alarm system without going through a monitoring company like ADT. The extensive documentation from Impassa covers how to wire and configure the device, and as long as the system isn’t locked when you get it, it seems like wiping the configuration and starting from scratch isn’t a problem.
If it’s possible to put together your own homebrew alarm system with one of these units at the core, then it seems the least we can do is take it apart and see what kind of potentially modifiable goodies are waiting under that shiny plastic exterior.
Reach Out and Touch Someone
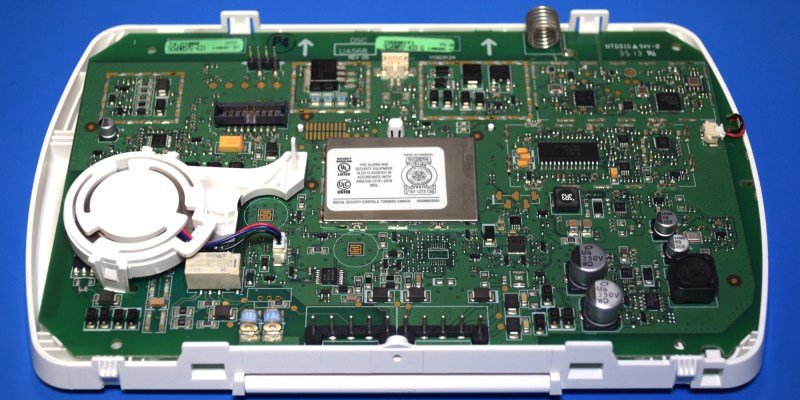
The SCW9057G-433 comes apart in two pieces with a bit of coercion around the edges, with the battery and 3G2075 “Alarm Communicator” board on the rear and the main PCB on the front. Or, at least, there should be a battery in the rear compartment. Our particular specimen has been robbed of its backup power, so you’ll have to use your imagination.
As we can see the cellular communications board features a SIM slot (with an unpopulated spot for a second), an external antenna, and an HE863-NAR 3G module that’s capable of pulling a respectable 7.2 Mbps over HSPA and features voice and SMS support. I didn’t expect there to be much else interesting on the 3G2075, but pulling open the RF shield revealed an unexpectedly large microcontroller.
The STM32F217VGT6 packs a 120 MHz ARM Cortex-M3 CPU and an impressive array of capabilities, including built-in Ethernet and USB. It’s not immediately clear why such a powerful chip is necessary to facilitate communications between the main PCB and the HE863-NAR, though its hardware accelerated encryption capabilities are potentially being put to use. Next to the MCU is a 16 Mb AT45DB161D serial flash chip, which under normal circumstances I would assume held the chip’s firmware. But since the STM32F217VGT6 already has fairly ample onboard flash, it seems more likely it’s being used to hold configuration data.
Chips Ahoy!
In this series of teardowns, we’re often confronted with some unfortunate realities, such as the fact that epoxy blobs and unmarked ICs are so common these days that it’s nearly the norm. I usually consider myself lucky if it’s possible to identify one or two of the chips on the board, especially if they’re the important ones. But as luck would have it, the main board of the SCW9057G-433 is packed full of recognizable ICs.
There’s a dizzying array of components here, but with a close eye we can see that the board is laid out quite logically, making it relatively easy to break down the different functional blocks. Especially since so many of the parts were obviously intended to be cordoned off from each other with snap-on RF shields, even if in the end most of them didn’t actually get installed. For example, by looking at where the coil antenna at the top of the board terminates, we can see the hardware responsible for 433 MHz communications.
One half of the equation is an Atmel ATA5428 ASK/FSK transceiver, which has a maximum data rate of 20 Kbit/s and can operate at either 433 or 868 MHz. In this case, the radio is paired with a PIC24FJ64GA002 microcontroller in a QFN28 package which appears to be running at 32 MHz by the looks of the nearby external oscillator.
Directly below that, and right next to where a speaker is plugged in, we find a slightly incongruous SOIC28 chip labeled U4082B. Located next to a MAX9730E 2.4 watt mono amplifier and a pair of MCP6002 op amps, at first I thought it might be some kind of audio alarm IC. But actually it’s a speakerphone chip that, among other things, is responsible for detecting when the user is speaking. Sure enough, a two-way speakerphone is listed as one of the features of the SCW9057G-433, presumably to be used so a representative of the monitoring company can speak to the customer directly through the alarm panel.
Old Reliable
It seems you can’t go more than a few millimeters on this board before you run into another IC to look up, but of course, there’s only so many voltage regulator spec sheets you can read in a day. So let’s pull off the RF shield and check out the real star of the show.
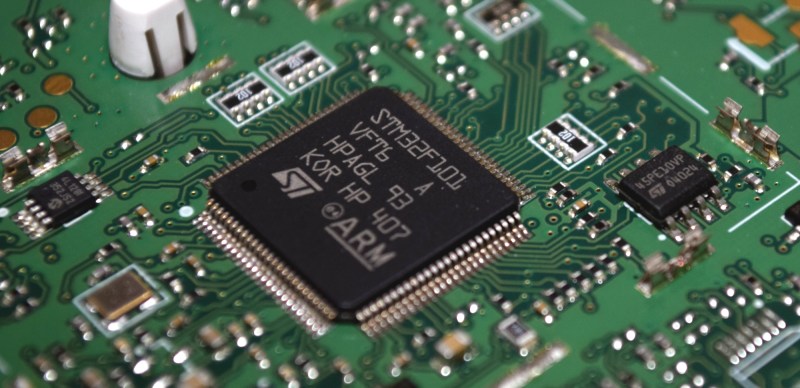
Here we can see a trio of chips in their natural habitat. In the center we have the STM32F101VF, a considerably less capable relative of the STM32F217 used in the communication board. The 36 MHz ARM Cortex-M3 chip doesn’t have nearly the bells and whistles of the newer F2 series, but it’s a reliable workhorse that Impassa likely has experience with from previous products. To the right of it we see an ST-branded 45PE10VP 1 Mb serial flash chip, and to the left, a Microchip 24LC128 128 K I2C EEPROM. Between the two external chips and the 768 Kb onboard the STM32F101VF, it seems the system has plenty of room to grow.
Incidentally, back in 2018 Aaron Christophel cracked open a robotic vacuum and found a very similar MCU. As we’ve come to expect from the prolific hacker, he started working on a his own firmware for the cleaning bot, part of which involved getting the chip working in the Arduino environment. It’s not clear how far he took the concept, but it at least establishes precedent should anyone want to take on the challenge of creating a custom firmware for this unit.
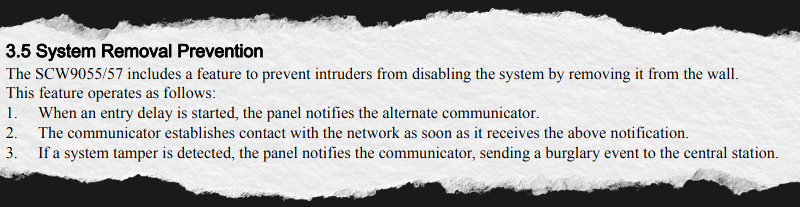
Tamper Resistant Packaging
The particularly keen-eyed reader may have already noticed it, but before closing out this teardown, I wanted to point out an interesting little feature of the SCW9057G-433: the tamper detectors. This capability is actually referenced in section 3.5 of the manual, and is described as a way for the unit to determine if somebody has tried to remove it from the wall.
Much like the VeriFone MX 925CTLS that I liberated from a defunct Toys R’ Us back in 2018, this is accomplished using a series of strategically placed plungers that push against traces on the PCB. Essentially it’s an open-air momentary push button that’s held closed so long as the device’s case isn’t opened. There’s one pad on the rear of the communications board, and two of them on the main PCB.
The first one is attached to a little lever that’s pushed when the SCW9057G-433 is screwed to the wall, so that the alarm will sound should anyone remove it. The central pad on the front PCB corresponds to a stalk attached to the rear plate of the case, which is clearly to alert the system if the panel has been opened. The third pad doesn’t have any obvious mate, so I can only assume its counterpart would be mounted to the battery, or perhaps some chassis component that holds it in. This would let the system detect if somebody was clever enough to try and cut the battery out from the side of the panel while it was still on the wall.

Second Life, or Good Enough?
We’ve got a bunch of identifiable chips, a microcontroller that we’ve already seen programmed via the Arduino IDE, and some pretty blatant programming headers. So what’s holding back an open source replacement firmware for the SCW9057G-433?
Well, for one thing there’s still a lot of reverse engineering you’d need to do before you could make a truly functional firmware. Getting the MCU to talk to the LCD and keypad probably wouldn’t be a problem, but that’s just scratching the surface. If you feel like giving it a go, we’ve covered some STM32 reverse engineering which should get you going in the right direction.
That said, the bigger problem might simply be that a custom firmware isn’t really needed for this device. The documentation from Impassa seems exceptional, and unless you’re unlucky enough to get one of these units that’s been locked by the previous user or installer, you should have free rein to pair it with your devices and configure it however you see fit.
As much as we love seeing proprietary code being obliterated by the glorious light of open source software here at Hackaday, I’ll admit that occasionally you have to pick your battles. Though just to be safe, I might ask Aaron Christophel if he wants a new toy to play with.
The device you see here was graciously provided to us by one of our wonderful readers. If you have an interesting piece of hardware that’s just taking up space around the shop and would like to donate it towards our ongoing series of teardowns, anonymously or otherwise, don’t hesitate to drop us a line.
























I have one of these when we moved in and the previous owner won’t give us the code. Tried common codes but no luck getting access to my alarm system. I don’t want to pay ADT to erase it and reprogram the whole thing. Would like to monitor it myself.
I thought you could wire a relay to the siren and pick up the signal there for unauthorized access.
Anyone with better ideas?
ADT typically sets the install code by the last four of the account number to the client. Also they wouldn’t reprogram it even if they wanted to since 3G is pretty much gone. If it were me I would replace the whole thing. 2GIG, Qolsys and Resiedo have much better panels. If you have a wired system you can just use some esp8266 to monitor the sensors.
While I am thinking of it. The default installer code is 5555 but ADT changes it.
Thanks for the suggestions. I probably tried that code along with local installer codes from Reddit. I will look into replacing it with an arduino/RasPi combo maybe. ESPs are a pain and would not be the best for a web server (dev/maintenance).
Better hurry, 3G is being shut down by all major carriers in 2022. Seems a better solution for OpenSource would be a microcontroller with WiFi connection to send email or text messages. Then you only have to worry about your internet connection being disabled by a savvy home invader cutting your cable or landline. Maybe put fake stickers proclaiming 5G security system on premises. The major stumbling block for most folks is tapping in to the hard wired system installed in houses built in the 1960s-2000s. Why install new sensors when suitable sensors are already hard wired and very reliable.
The solution to the landline attack worry is to rent a cheap webserver from digitalOcean or similar (or use a tiny bit of the capability for one you already rent for webpage hosting) for a heartbeat with your security hub. If it doesn’t see the heartbeat, that means either your hub’s internet is out (whether malicious, ISP issues or home network issues) or your hub is malfunctioning. It looks like there are already a few home security projects available for the RPi, which would be a natural choice for a hub to me.
Good idea
Good idea
Sadly you don’t need to be that tech savvy to disable t’internet. In the uk at least, there is often a tail coming out of a hole in the ground and terminating in a grey wall box. With the new fibre we have just had installed, one snip and broadband and ‘phone lines are down.
The reason for cell primary in modern alarm panels is not just to get rid of the tie to landline, but to get rid of any ties to premises comms completely. Customer pays alarm bill, they get monitoring. Don’t need to worry about supplying phone line – panel always works.
Another change in recent years in the industry is the move to these all-in-one panels, which primarily use wireless sensors. Some models have the ability to change radios – when the 3G phaseout started, 4G swaps became available.
Internet isn’t used as primary comms. First, isn’t seen as “reliable,” and second, it’s on-prem comms with way more potential for config problems than an old POTS line takeover. If you see Ethernet on a modern panel it isn’t usually for reporting (though some will do it as a failover) but rather for faster response when using home automation type integration such as Alarm.com.
Re: this panel, DSC loves to use ST micros. Pretty much their entire lineup no matter the family uses them, from alarm panels to keypads to whatever else. They also like to use either Atmel or TI radio chips. I think PowerG is a TI radio and an MSP430 to control it.
“Located next to a MAX9730E 2.4 watt mono amplifier and a pair of MCP6002 op amps, at first I thought it might be some kind of audio alarm IC. But actually it’s a speakerphone chip that, among other things, is responsible for detecting when the user is speaking. Sure enough, a two-way speakerphone is listed as one of the features of the SCW9057G-433, presumably to be used so a representative of the monitoring company can speak to the customer directly through the alarm panel.”
Our old alarm has the ability to “listen” for audible alarms placed around the house. The installer also demonstrated it can pick up voices in most of the house. His example was too show that if one was trapped in the basement during an alarm, they could just tell the Call Center where to direct rescuers.
But our alarm is land line, not cellular.
I have a GE system, and when I was locked out of it, I was actually able to pull the EEPROM out, and some nice people on the internet had already done the legwork to find the bits where the code was stored. The EEPROM on my system was actually designed to be removed from its socket- no desoldering required. I am guessing something similar can be done here?
I do actually plan on pulling the flash chips off the board and seeing if I can read what they contain, as much for my own curiosity as anything.
ADT, a firm so reputable that I used to block (at work) *any* email that had ADT in the subject line. They didn’t care where or how they got your money & paid referral fees to spammers who spewed thousands of “get ADT” emails a day. Think about .4 FTE as a spam filter admin…
Heh.
I’m currently (as in…have an Arduino hooked up on the table next to me) monitoring the comms line between my “FBII STAR XL 4800 EZ” alarm panel and its keypad. It’s designed to hook up to a POTS line, but I thought most of the information I want is being sent over a serial line, so why not tap into that? 1920 baud, 8N1 standard serial. 12VDC open collector multidrop. I’m logging and timestamping the messages, have masked ut the ones that repeat, and am now working on sending new messages to my phone via my cell provider’s email to SMS gateway.