Looking up at the sky just after sunset or just before sunrise will reveal a fairly staggering amount of satellites orbiting overhead, from tiny cubesats to the International Space Station. Of course these satellites are always around, and even though you’ll need specific conditions to view them with the naked eye, with the right radio antenna and only a few dollars in electronics you can see exactly which ones are flying by at any time.
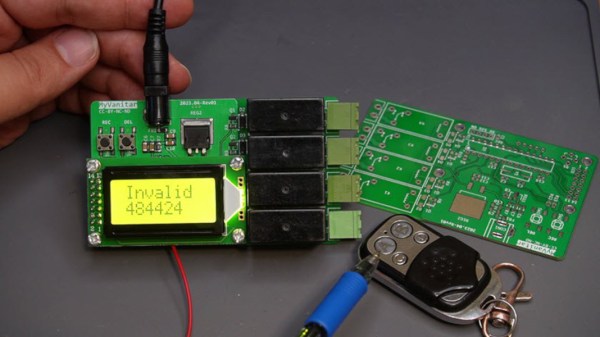
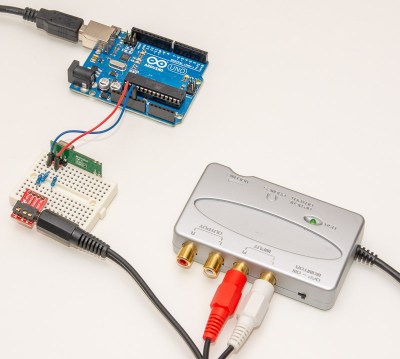
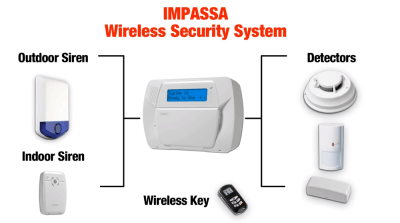
[Josh] aka [Ham Radio Crash Course] is demonstrating this build on his channel and showing every step needed to get something like this working. The first part is finding the correct LoRa module, which will be the bulk of the cost of this project. Unlike those used for most Meshtastic nodes, this one needs to be built for the 433 MHz band. The software running on this module is from TinyGS, which we have featured here before, and which allows a quick and easy setup to listen in to these types of satellites. This build goes much further into detail on building the antenna, though, and also covers some other ancillary tasks like mounting it somewhere outdoors.
With all of that out of the way, though, the setup is able to track hundreds of satellites on very little hardware, as well as display information about each of them. We’d always favor a build that lets us gather data like this directly over using something like a satellite tracking app, although those do have their place. And of course, with slightly more compute and a more directed antenna there is all kinds of other data beaming down that we can listen in on as well, although that’s not always the intent.