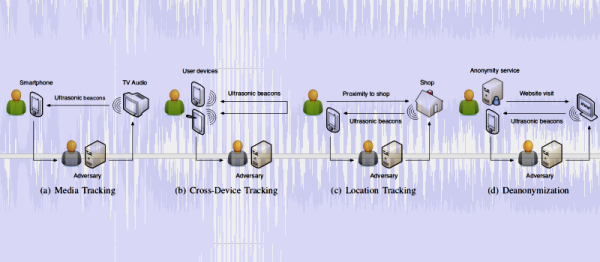
An ultrasonic beacon is an inaudible sound with encoded data that can be used by a listening device to receive information on just about anything. Beacons can be used, for example, inside a shop to highlight a particular promotion or on a museum for guided tours where the ultrasonic beacons can encode the location. Or they can be used to track people consumers. Imagine if Google find outs… oh, wait… they already did, some years ago. As with almost any technology, it can be used to ‘do no harm’ or to serve other purposes.
Researchers from the Technische Universitat Braunschweig in Germany presented a paper about Ultrasonic Side Channels on Mobile Devices and how can they be abused in a variety of scenarios , ranging from simple consumer tracking to deanonymization. These types of ultrasonic beacons work in the 18 kHz – 20 kHz range, which the human being doesn’t have the ability to hear, unless you are under twenty years old, due to presbycusis. Yes, presbycusis. This frequency range can played via almost any speaker and can be picked up easily by most mobile device microphones, so no special hardware is needed. Speakers and mics are almost ubiquitous nowadays, so there is a real appeal to the technology.