Why is it always a helium leak? It seems whenever there’s a scrubbed launch or a narrowly averted disaster, space exploration just can’t get past the problems of helium plumbing. We’ve had a bunch of helium problems lately, most famously with the leaks in Starliner’s thruster system that have prevented astronauts Butch Wilmore and Suni Williams from returning to Earth in the spacecraft, leaving them on an extended mission to the ISS. Ironically, the launch itself was troubled by a helium leak before the rocket ever left the ground. More recently, the Polaris Dawn mission, which is supposed to feature the first spacewalk by a private crew, was scrubbed by SpaceX due to a helium leak on the launch tower. And to round out the helium woes, we now have news that the Peregrine mission, which was supposed to carry the first commercial lander to the lunar surface but instead ended up burning up in the atmosphere and crashing into the Pacific, failed due to — you guessed it — a helium leak.
Continue reading “Hackaday Links: September 1, 2024”
leak13 Articles
On An Aging Space Station, Air Leaks Become Routine
Anyone who’s ever owned an older car will know the feeling: the nagging worry at the back of your mind that today might be the day that something important actually stops working. Oh, it’s not the little problems that bother you: the rips in the seats, the buzz out of the rear speakers, and that slow oil leak that might have annoyed you at first, but eventually just blend into the background. So long as the car starts and can get you from point A to B, you can accept the sub-optimal performance that inevitably comes with age. Someday the day will come when you can no longer ignore the mounting issues and you’ll have to get a new vehicle, but today isn’t that day.
Looking at developments over the last few years one could argue that the International Space Station, while quite a bit more advanced and costly than the old beater parked in your driveway, is entering a similar phase of its lifecycle. The first modules of the sprawling orbital complex were launched all the way back in 1998, and had a design lifetime of just 15 years. But with no major failures and the Station’s overall condition remaining stable, both NASA and Russia’s Roscosmos space agency have agreed to several mission extensions. The current agreement will see crews living and working aboard the Station until 2030, but as recently as January, NASA and Roscosmos officials were quoted as saying a further extension isn’t out of the question.
Still, there’s no debating that the ISS isn’t in the same shape it was when construction was formally completed in 2011. A perfect case in point: the fact that the rate of air leaking out of the Russian side of the complex has recently doubled is being treated as little more than a minor annoyance, as mission planners know what the problem is and how to minimize the impact is has on Station operations.
Continue reading “On An Aging Space Station, Air Leaks Become Routine”
Damaged Soyuz May Leave Crew Without A Ride Home
Though oddly beautiful in its own way, it’s a sight no astronaut wants to see: their spacecraft, the only way they have to return to Earth, ejecting countless iridescent droplets of something into space.
When the crew of Apollo 13 saw their craft literally bleeding out on their trip to the Moon it was clear the mission, and ultimately their lives, were in real jeopardy. Luckily the current situation is not nearly as dire, as the leaking Soyuz MS-22 spacecraft docked to the International Space Station doesn’t pose any immediate danger to those aboard the orbiting laboratory. But it’s still an unprecedented situation, and getting its crew home will require engineers on the ground to make some very difficult decisions.
This situation is still developing, and neither NASA nor their Russian counterpart Roscosmos have released much in the way of specifics. But we can make some educated guesses from the video and images we’ve seen of the stricken Soyuz capsule, and from what’s been shown to the public so far, things aren’t looking good.
Continue reading “Damaged Soyuz May Leave Crew Without A Ride Home”
A Water Leak Detector That Listens Carefully
Water leaks can be pernicious things. Even just a few drips per minute happening undetected inside a wall can cause major damage if left unrepaired for long enough. AquaPing is a new device that hopes to detect difficult-to-find water leaks with the aid of acoustic methods.
The AquaPing is a so-called “stand-off” sensor that is intended to detect leaks at a distance, even if they are inside a wall. No contact is needed with the plumbing itself. Instead, the device detects the broadband high-frequency noise created when water leaks from a pipe under pressure.
It’s a method that’s best suited to leaks from cracks or loose fittings. These generate a characteristic hiss that can be picked up with signal analysis even if the noise itself is obscured to human perception by other noises in the area. However, leaks like a hole in a gutter or a dripping rusted-out water tank are best found by other methods, as they don’t create this same signature noise.
The device will soon be launched on CrowdSupply as a purchasable product, however the project is fully open source for those eager to dive in themselves. We’ve featured some other really creative leak detectors before, too! Video after the break.
Continue reading “A Water Leak Detector That Listens Carefully”
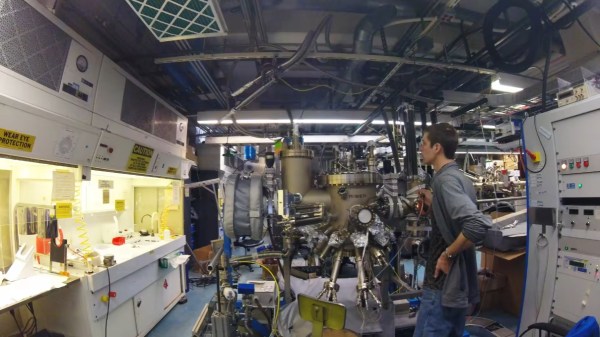
Solving Ultra High Vacuum Leaks Has An Elementary Solution
When we think of a vacuum leak we generally think of a car that just doesn’t want to run quite right. Most normally aspirated internal combustion engines rely on the vacuum created by the pistons to draw in the air fuel mixture that’s produced by the carburetor or fuel injection system. Identifying the leak usually involves spraying something combustible around common trouble areas while the engine is running. Changes to the engine speed indicate when the combustible gas enters the intake manifold and the leak can be found.
What if your vacuum leak is in a highly specialized piece of scientific equipment where the pressures are about 12 times orders of magnitude lower than atmospheric pressure, and the leak is so small it’s only letting a few atoms into the vacuum chamber at a time? [AlphaPhoenix] takes dives deep into this very subject in his video “Air-tight vs. Vacuum-tight.” which you can watch below the break.
Not only does [AlphaPhoenix] discuss how a perfect pressure vessel is sealed, he also explains the specialized troubleshooting methods used which turn out not to be all that different from troubleshooting an automotive vacuum leak- only in this case, several magnitudes more complex and elemental in nature.
We also enjoyed the comments section, where [AlphaPhoenix] addresses some of the most common questions surrounding the video: Torque patterns, the scarcity of the gasses used, and leaving well enough alone.
Does talking about vacuums get you pumped? Perhaps you’d enjoy such vacuum hacks as putting the toothpaste back in the tube in your homemade vacuum chamber.
Thank you [Morgan] for sending this one in. Be sure to send in your own hacks, projects, and fantastic finds through the Tip Line!
Continue reading “Solving Ultra High Vacuum Leaks Has An Elementary Solution”
Ask Hackaday: Is Windows XP Source Code Leak A Bad Thing?
News comes overnight that the Windows XP source code has been leaked. The Verge says they have “verified the material as legitimate” and that the leak also includes Windows Server 2003 and some DOS and CE code as well. The thing is, it has now been more than six years since Microsoft dropped support for XP, does it really matter if the source code is made public?
The Poison Pill
As Erin Pinheiro pointed out in her excellent article on the Nintendo IP leak earlier this year (perhaps the best Joe Kim artwork of the year on that one, by the way), legitimate developers can’t really make use of leaked code since it opens them up to potential litigation. Microsoft has a formidable legal machine that would surely go after misuse of the code from a leak like this. Erin mentions in her article that just looking at the code is the danger zone for competitors.
Even if other software companies did look at the source code and implement their own improvements without crossing the legal line, how much is there still to gain? Surely companies with this kind of motivation would have reverse engineered the secret sauce of the long dead OS by now, right?
Spy vs. Spy
The next thing that comes to mind are the security implications. At the time of writing, statcount pegs Windows XP at a 0.82% market share which is still going to be a very large number of machines. Perhaps a better question to consider is what types of machines are still running it? I didn’t find any hard data to answer this question, however there are dedicated machines like MRIs that don’t have easy upgrade paths and still use the OS and there is an embedded version of XP that runs on point-of-sale, automated teller machines, set-top boxes, and other long-life hardware that are notorious for not being upgraded by their owners.
Continue reading “Ask Hackaday: Is Windows XP Source Code Leak A Bad Thing?”
No, The Nintendo Leak Won’t Help Emulator Developers, And Here’s Why
If you haven’t heard from other websites yet, earlier this year a leak of various Nintendo intellectual properties surfaced on the Internet. This included prototype software dating back to the Game Boy, as well as Verilog files for systems up to the Nintendo 64, GameCube and Wii. This leak seems to have originated from a breach in the BroadOn servers, a small hardware company Nintendo had contracted to make, among other things, the China-only iQue Player.
So, that’s the gist of it out of the way, but what does it all mean? What is the iQue Player? Surely now that a company’s goodies are out in the open, enthusiasts can make use of it and improve their projects, right? Well, no. A lot of things prevent that, and there’s more than enough precedent for it that, to the emulation scene, this was just another Tuesday.
Continue reading “No, The Nintendo Leak Won’t Help Emulator Developers, And Here’s Why”