Things are not looking good for iRobot. Although their robotic Roomba vacuums are basically a household name, the company has been faltering financially for some time now. In 2024 there was hope of a buyout by Amazon, who were presumably keen to pull the bots into their Alexa ecosystem, but that has since fallen through. Now, by the company’s own estimates, bankruptcy is a very real possibility by the end of the year.
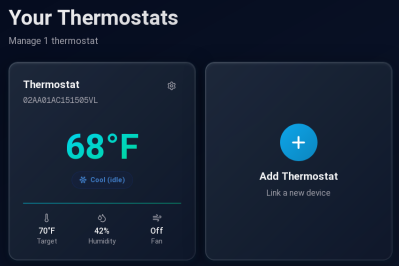
 Hackaday isn’t a financial blog, so we won’t get into how and why iRobot has ended up here, although we can guess that intense competition in the market probably had something to do with it. We’re far more interested in what happens when those millions of domesticated robots start getting an error message when they try to call home to the mothership.
Hackaday isn’t a financial blog, so we won’t get into how and why iRobot has ended up here, although we can guess that intense competition in the market probably had something to do with it. We’re far more interested in what happens when those millions of domesticated robots start getting an error message when they try to call home to the mothership.
We’ve seen this scenario play out many times before — a startup goes belly up, and all the sudden you can’t upload new songs to some weirdo kid’s media player, or the gadget in your fridge stops telling you how old your eggs are. (No, seriously.) But the scale here is unprecedented. If iRobot collapses, we may be looking at one of the largest and most impactful smart-gadget screw overs of all time.
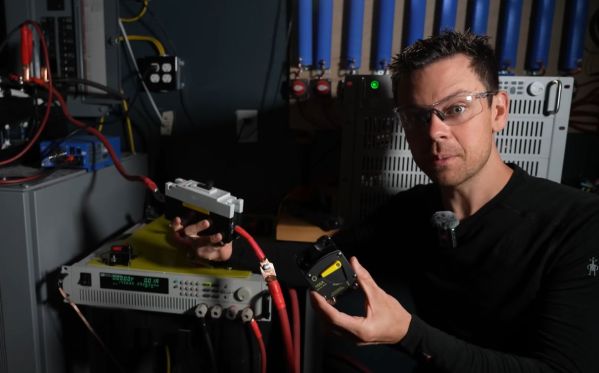
Luckily, we aren’t quite there yet. There’s still time to weigh options, and critically, perform the kind of research and reverse engineering necessary to make sure the community can keep the world’s Roombas chugging along even if the worst happens.
Continue reading “If IRobot Falls, Hackers Are Ready To Wrangle Roombas”