Submarines have always been about stealth; that’s always been the whole point of putting them underwater. Tracking them can be difficult, even to this day, but China may have a new technique to help in this endeavour, as reported by the South China Morning Post.

The news comes from a study published in a Chinese journal, regarding detection of the most advanced American submarines. The stealthiest examples use all kinds of sophisticated systems to damp vibrations and reduce acoustic signatures to make detection as hard as possible. However, a new type of magnetic detector could change all that.
A research team used computer simulations to determine whether nuclear-powered submarines could be detected via the bubbles produced when cruising at high speed underwater. When these bubbles inevitably collapse, it can apparently produce a detectable signal that is orders of magnitude higher than the sensitivity of the best magnetic anomaly detectors. The signal is found on the order of 34.19 to 49.94 Hz, deep in the ELF range, according to researchers.
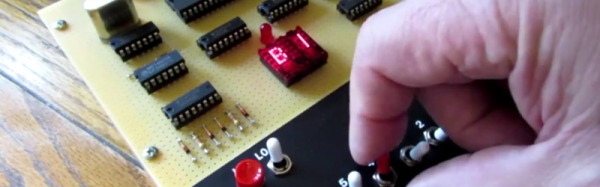
This could yet create another arms race, as submarine designers begin designing vessels to reduce bubble shedding at speed. Or, for all we know, this is already a well-known principle in the high-stakes world of submarine surveillance and combat. If you’re in the know, please don’t reveal any classified information in the comments section. It’s not worth your job or ours! If you recreate such a detector at home in a non-treasonous manner, though, don’t hesitate to let us know!