Do you remember the early days of consumer wireless networking, a time of open access points with default SSIDs, manufacturer default passwords, Pringle can antennas, and wardriving? Fortunately out-of-the-box device security has moved on in the last couple of decades, but there was a time when most WiFi networks were an open book to any passer-by with a WiFi-equipped laptop or PDA.
The more sophisticated wardrivers used directional antennas, the simplest of which was the abovementioned Pringle can, in which the snack container was repurposed as a resonant horn antenna with a single radiator mounted on an N socket poking through its side. If you were more sophisticated you might have used a Yagi array (a higher-frequency version of the antenna you would use to receive TV signals). But these were high-precision items that were expensive, or rather tricky to build if you made one yourself.
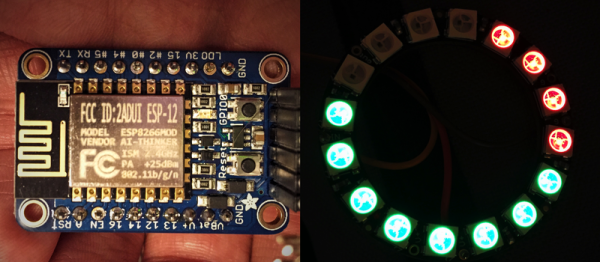
In recent years the price of commercial WiFi Yagi arrays has dropped, and they have become a common sight used for stretching WiFi range. [TacticalNinja] has other ideas, and has used a particularly long one paired with a high-power WiFi card and amplifier as a wardriver’s kit par excellence, complete with a sniper’s ‘scope for aiming.
The antenna was a cheap Chinese item, which arrived with very poor performance indeed. It turned out that its driven element was misaligned and shorted by a too-long screw, and its cable was rather long with a suspect balun. Modifying it for element alignment and a balun-less short feeder improved its performance no end. He quotes the figures for his set-up as 4000mW of RF output power into a 25dBi Yagi, or 61dBm effective radiated power. This equates to the definitely-illegal equivalent of an over 1250W point source, which sounds very impressive but somehow we doubt that the quoted figures will be achieved in reality. Claimed manufacturer antenna gain figures are rarely trustworthy.
This is something of an exercise in how much you can push into a WiFi antenna, and his comparison with a rifle is very apt. Imagine it as the equivalent of an AR-15 modified with every bell and whistle the gun store can sell its owner, it may look impressively tricked-out but does it shoot any better than the stock rifle in the hands of an expert? As any radio amateur will tell you: a contact can only be made if communication can be heard in both directions, and we’re left wondering whether some of that extra power is wasted as even with the Yagi the WiFi receiver will be unlikely to hear the reply from a network responding at great distance using the stock legal antenna and power. Still, it does have an air of wardriver chic about it, and we’re certain it has the potential for a lot of long-distance WiFi fun within its receiving range.
This isn’t the first wardriving rifle we’ve featured, but unlike this one you could probably carry it past a policeman without attracting attention.