These days everything needs to be connected to remote servers via the internet, whether it’s one’s TV, fridge or even that new car you just bought. A recently discovered (and already patched) vulnerability concerning Kia cars was a doozy in this regard, as a fairly straightforward series of steps allowed for any attacker to obtain the vehicle identification number (VIN) from the license plate, and from there become registered as the car’s owner on Kia’s network. The hack and the way it was discovered is described in great detail on [Sam Curry]’s website, along with the timeline of its discovery.
Notable is that this isn’t the first vulnerability discovered in Kia’s HTTP-based APIs, with [Sam] this time taking a poke at the dealer endpoints. To his surprise, he was able to register as a dealer and obtain a valid session ID using which he could then proceed to query Kia’s systems for a user’s registered email address and phone number.
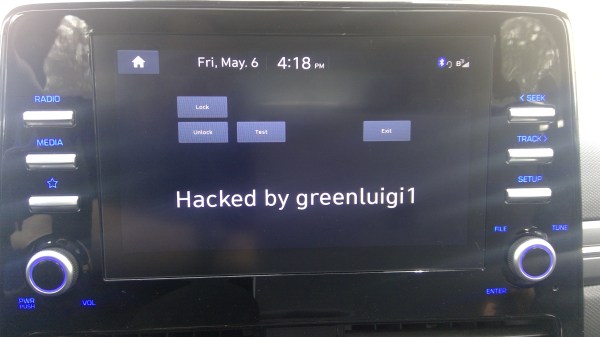
With a specially crafted tool to automate the entire process, this information was then used to demote the car’s owner and register the attacker as the primary owner. After this the attacker was free to lock/unlock the doors, honk to his heart’s content, locate the car and start/stop the vehicle. The vulnerability affected all Kia cars made after 2013, with the victim having no indication of their vehicle having been hijacked in this manner. Aside from the doors randomly locking, the quaint honking and engine turning on/off at a whim, of course.
Perhaps the scariest part about this kind of vulnerability is that it could have allowed an attacker to identify a vulnerable parked car, gained access, before getting into the car, starting the engine and driving away. As long as these remote APIs allow for such levels of control, one might hope that one day car manufacturers will take security somewhat more serious, as this is only the latest in a seemingly endless series of amusingly terrifying security vulnerabilities that require nothing more than some bored hackers with HTTP query crafting tools to discover.
Continue reading “Hacking Kia: Remotely Hijack A Car Using Only Its License Plate”