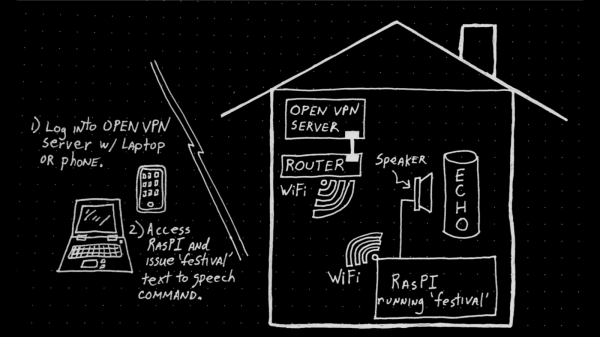
Let’s not pretend we aren’t all guilty of it: at some point we’ve all connected to a public WiFi network to check our email or log into some site or service. We know the risks, we know better. But in a weak moment we can let the convenience of that public network get the better of us. What if you had a small secure router that you could use as an encrypted VPN endpoint, allowing you to connect to those enticing public networks while keeping your traffic secure? That’s precisely what [David] had in mind when he built this pint-sized solar-powered OpenWRT router.
 At the heart of this gadget is the TP-Link TL-MR3020, a tiny OpenWRT-compatible router that’s no stranger to the pages of Hackaday. Its small size and low cost have made it a natural choice for a wide array of projects, so it’s little surprise that [David] gravitated towards it. But simply getting OpenWRT installed on the MR3020 and configuring OpenVPN doesn’t exactly grant you entrance into the Hackaday Pantheon, so obviously there’s a bit more to the story.
At the heart of this gadget is the TP-Link TL-MR3020, a tiny OpenWRT-compatible router that’s no stranger to the pages of Hackaday. Its small size and low cost have made it a natural choice for a wide array of projects, so it’s little surprise that [David] gravitated towards it. But simply getting OpenWRT installed on the MR3020 and configuring OpenVPN doesn’t exactly grant you entrance into the Hackaday Pantheon, so obviously there’s a bit more to the story.
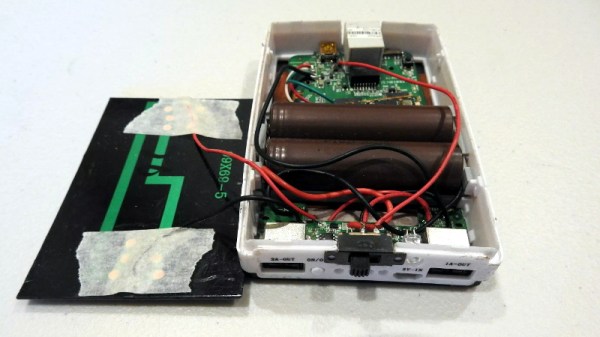
For one, [David] didn’t like the idea of a USB flash drive hanging out of the side of his router. Since the flash drive would essentially be a permanent part of the router, as it is being used to expand the rather meager internal storage of the MR3020 he decided to wack the USB end off the flash drive and solder it directly to the router’s PCB. This gave him a much cleaner looking package, but it still wasn’t as portable as he’d like.
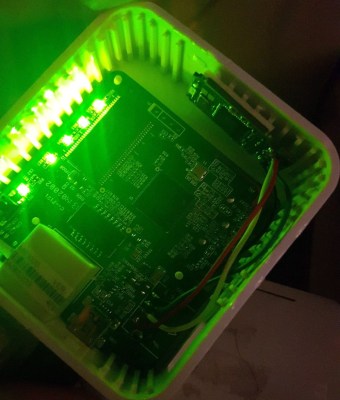
He decided to order a solar-charged USB power bank to become the new home of his hacked MR3020. He kept the solar panel and charge controller from the original gadget, and after some researched settled on a pair of LG-HG2 3000 mAh batteries as the power source. [David] went through a few charge and discharge cycles making sure everything worked as expected before buttoning up the case. In the future he says he might transplant the electronics into a 3D printed case, but for now he’s pretty pleased with the results.
If you’d like to try your hand at hacking these popular micro routers, you’ll need to start with an OpenWRT firmware. After you’ve got a full blown Linux distro running on this little fellow, the only limitation is your own imagination.